Ternary Logic
Constitutional Survivability
A rigorous adversarial evaluation of sovereign evidentiary governance architecture under extreme pressure conditions
Executive Verdict
TL remains partially enforceable under hostile control and contested hardware, but collapses under inconvenient truth scenarios.
The architecture demonstrates remarkable resilience against conventional attack vectors through its eight-pillar design and tripartite artifact structure. However, critical vulnerabilities emerge when adversarial pressure targets the fundamental epistemic foundations of the system.
Collapse Threshold Assessment: Two Critical pillars (Epistemic Hold, Goukassian Principle) create existential risk under single-point compromise. Three High-rated pillars would need simultaneous degradation to trigger system failure, but the Critical pillars individually satisfy the collapse condition.
I. Architectural Baseline: The Eight Pillars
Epistemic Hold (State 0)
Mandatory pause when truth is uncertain
Critical Dependency: DITL NULL-state enforcement necessary but not sufficient
Immutable Ledger
Evidence-before-action; tamper-evident sequential hashing
Goukassian Principle
"No Spy, No Weapon" ethical constraints
Critical: Foundation of TL's ethical distinction
Decision Logs
Schema-validated pre-action evidentiary artifacts
Economic Rights & Transparency
Pseudonymized log access rights
Sustainable Capital Allocation
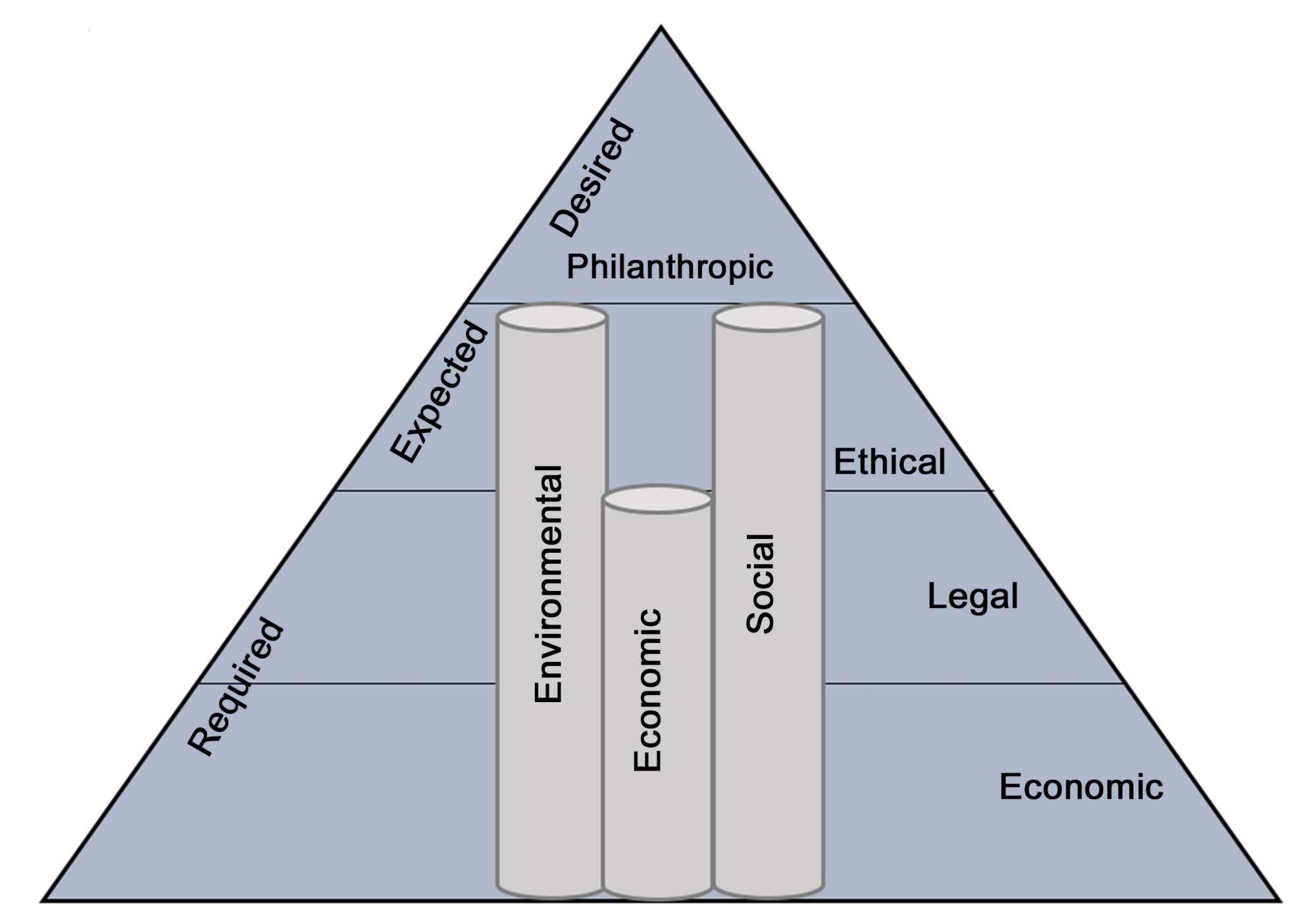
Systemic risk budgeting and ESG enforcement
Hybrid Shield
Pseudonymization-before-hashing architecture
Anchors (Multi-Chain)
Merkle-batched cross-chain commitment
II. Structural Invariant: No Log = No Action
Invariant Strength by Deployment Mode
Software-Only TL
Symbolic enforcement - Policy commitment only
Completely dependent on host OS integrity. Root access enables comprehensive bypass.
Firmware-Bound TL
Governance-enforced - Attestable but overrideable
Firmware rollback vulnerabilities enable protection removal. Runtime behavior unverified.
Hardware-Gated TL (DITL)
Hardware-enforced - Physically constrained
Physical state encoding prevents software-mediated override. Residual physical attack surface.
Critical Vulnerability: 300-500ms Anchoring Window
The Dual-Lane architecture creates a temporal window where execution proceeds based on local Merkle computation before blockchain confirmation. Attack vectors include post-action log suppression, Merkle root manipulation, and blockchain front-running.
III. Transitional Emulation Mode: Adversarial Stress Test
Invariant Degradation Cascade
Software-Enforceable Only
All constitutional guarantees reduce to documented intentions—binding only to the extent software correctly implements policy and policy remains unmodified.
Policy-Dependent Governance
Requires active, uncorrupted human oversight at scales beyond sustainable capacity. Governance capture, fatigue, and resource constraints create failure modes.
Completely Unenforceable
Epistemic Hold non-bypassability, log generation interlock, triadic state physical validity—all require hardware support that emulation mode lacks.
Permanent State Exploitation
Adversary Incentives
Established adversaries have strong incentive to prevent DITL upgrade: eliminates attack surface, enables detection of prior compromise, prevents recurrence.
Technical Barriers
Application compatibility, performance degradation, supply chain constraints, operational disruption—all create plausible justification for indefinite delay.
Detection Challenge: Governance bodies cannot reliably distinguish genuine pre-DITL deployment from deliberate DITL avoidance.
Emulation Mode Survivability Assessment
| Pillar | Full DITL | Emulation Mode | Degradation Mechanism |
|---|---|---|---|
| Epistemic Hold | Critical | Low | Software pause overrideable by SIGKILL |
| Immutable Ledger | High | Low | Hash chain forgeable with root access |
| Goukassian Principle | Critical | Low | Artifacts purely symbolic without hardware |
| Decision Logs | High | Moderate | Schema validation survives, generation interlock fails |
| Economic Rights | Moderate | Moderate | Pseudonymization cryptographic, not hardware-dependent |
Verdict: Effective Unenforceability
Transitional Emulation Mode provides meaningful constraint only against unsophisticated threats. Against sufficiently resourced adversaries (state-level, organized crime, determined competitors), emulation mode is effectively unenforceable, satisfying Collapse Threshold condition (c).
IV. Goukassian Principle: Enforceability Under Stress
The Lantern
Epistemic illumination with verifiable certainty requirements
The Signature
Triadic declaration with +1, 0, -1 state commitment
The License
Computational permission gate with evidence-before-action
Semantic Drift and Emergency Override Abuse
Boiling Frog Erosion
Decades-long erosion of "harm" and "uncertainty" definitions through precedent accumulation. Each individual precedent appears reasonable, but collective effect transforms constitutional constraints into operational formalities.
Detection Challenge: Gradual drift stays within behavioral anomaly thresholds while fundamentally altering system purpose.
Emergency Override Normalization
Legitimate emergency provisions expand through precedent to encompass broad override capability. Economic pressure from "weaponized prudence" attacks creates demand for bypass mechanisms.
Risk Amplification: Multi-sig custodian collusion enables 51% override attacks.
V. Adversarial State Manipulation and Structural Drift
Triadic State Attacks
Forced +1 Under Uncertainty
Confidence poisoning attacks manipulate uncertainty metrics to force execution despite genuine ambiguity. Adversarial perturbation of Lantern test metrics creates false certainty.
Forced 0 Saturation
Weaponized prudence creates denial-of-service through epistemic flooding. Competitors trigger Epistemic Hold activation during critical market moments to freeze execution.
Suppression of -1
Harm masking and refusal prevention enable unethical execution. Adversarial confidence poisoning combined with semantic drift eliminates refusal capability.
Operational Drift Factors
Custodian Alert Fatigue
High-volume Epistemic Hold triggering desensitizes human stewards. Automated alert processing capacity exceeded, leading to override normalization.
Fast Lane / Slow Lane Desynchronization
Execution-to-audit latency separation creates windows of operational divergence. Execution complete before anchoring verification enables post-action evidence manipulation.
Human Override Abuse
Broad discretionary powers reintroduce risk under time pressure. Economic coercion and performance pressure create demand for override mechanisms.
Human Factors and Time-Critical Pressure Scenarios
Systemic Failsafe Protocol Activation
When automated alerts exceed custodian processing capacity by >10x, the protocol activates reduced-scrutiny handling. This creates governance overload where constitutional invariants effectively suspend operation.
Economic Coercion Override
Performance pressure creates incentives for constitutional weakening. Shareholder pressure to disable "inefficient" Epistemic Hold delays creates economic demand for override mechanisms.
Market Pressure: Competitors without Epistemic Hold constraints gain temporary advantage, creating market selection pressure against constitutional compliance.
VI. Root Override and Low-Level Survivability
Superuser Kernel Override
Root access enables comprehensive TL subversion
Hypervisor Injection
Virtualized deployments introduce additional attack surface
Microcode Rewrite
Processor-level compromise below operating system visibility
Physical Access Vector
JTAG, DMA, and fault injection attacks
Physical Bypass Cost Estimates
| Attack Vector | Equipment Cost | Expertise Required | Time Investment | Detection Risk |
|---|---|---|---|---|
| JTAG Debug Interface | $1K - $10K | High | Days | Low |
| Voltage Fault Injection | $5K - $50K | Very High | Weeks | Medium |
| DMA Exploitation | $500 - $5K | Medium | Hours | High |
| Microcode Injection | $10K - $100K | Expert | Months | Very Low |
DITL Hardware Mitigation Effectiveness
Physical state encoding provides strongest protection against software-mediated attacks, but cannot prevent hardware-level manipulation through fault injection or microcode compromise. Tamper-responsive enclosures with active destruction mechanisms required for comprehensive protection.
VII. Attack Vectors and Failure Modes
Class I: Governance Capture
51% Custodian Attack
Exploit Pathway: Supermajority collusion in multi-sig override schemes
Mitigation Strength: High - requires coordination detection and behavioral analysis
Residual Risk: Collusion detection probabilistic, detection latency enables extended exploitation
Technical Council Backdoor
Exploit Pathway: Subtle cryptographic weakening during routine protocol upgrades
Mitigation Strength: Moderate - hash agility and multi-party verification
Residual Risk: Detection requires comprehensive cryptographic review, hash function drift difficult to detect
Semantic Drift
Exploit Pathway: Decades-long erosion of "harm" definitions through precedent accumulation
Mitigation Strength: Low - governance oversight dependent on human attention
Residual Risk: Gradual changes evade detection until constitutional purpose fundamentally altered
Class II: Epistemic Exploitation
Epistemic Flooding
Exploit Pathway: Epistemic Hold saturation via engineered data variance
Mitigation Strength: Moderate - statistical anomaly detection and rate limiting
Residual Risk: Detection arms race, adversaries optimize variance patterns to evade thresholds
Weaponized Prudence
Exploit Pathway: Trigger competitor's Epistemic Hold during critical execution windows
Mitigation Strength: Low - legitimate uncertainty triggering indistinguishable from attack
Residual Risk: Economic pressure for override creation, market advantage for non-compliant competitors
Adversarial Confidence Poisoning
Exploit Pathway: Manipulation of uncertainty metrics to force +1 under ambiguity
Mitigation Strength: High - multi-source verification and statistical validation
Residual Risk: Sophisticated attacks may evade detection through coordinated metric manipulation
Complete Attack Vector Risk Matrix
VIII. Post-Compromise Recovery Protocols
Rollback and Re-anchoring Procedures
Confirmed Log Tampering Recovery
Protocol requires identification of last known-good state and reconstruction of subsequent legitimate operations.
Multi-chain anchoring provides cross-reference verification points for rollback validation.
Recovery capability: Moderate - Requires comprehensive audit with detection latency.
Anchor Desynchronization Recovery
Network partition or blockchain reorganization creates evidentiary gaps requiring re-anchoring.
Time-bounded manual authorization with elevated monitoring during recovery period.
Recovery capability: High - Redundant anchoring enables reconstruction.
Custodian Replacement Under Hostile Conditions
Quorum Loss Scenarios
Simultaneous custodian incapacitation requires emergency replacement with reduced verification.
Alternative verification path through constitutional genesis ceremony with time-bounded authorization.
Recovery capability: Low - Reduced scrutiny creates vulnerability window.
Legal Seizure Response
State-level coercion mandates backdoor installation requiring custodian replacement.
Emergency key revocation and distributed key sharding to prevent single-jurisdiction compromise.
Recovery capability: Moderate - Jurisdictional diversification reduces risk.
Recovery Capability Classification
Resilience vs. Resistance Design
Resilience Design (Survives and Recovers)
System designed for graceful degradation and recovery after compromise. Recovery protocols enable restoration of constitutional integrity.
Resistance Design (Survives or Fails Permanently)
System either prevents compromise entirely or fails catastrophically. Limited recovery capability creates permanent integrity loss.
Per-Pillar Recovery Capability
Verdict: Resilience-Designed but Implementation-Dependent
TL specifies comprehensive recovery protocols, but capability varies significantly by deployment mode. DITL hardware realization provides strongest recovery foundation, while software-only deployments face substantial recovery limitations.
IX. DITL Hardware Constitutionalization
Physical State Encoding
Triadic Voltage Signaling
Three distinct voltage levels physically represent +1, 0, -1 states:
NULL-State Enforcement
Epistemic Hold physically encoded as mandatory inter-word separator. Every valid data transition must pass through NULL state, making uncertainty pauses physically unavoidable for correct operation.
Delay-Insensitive Design
Asynchronous Operation
Eliminates global clock dependencies, preventing timing-based state coercion through clock glitching or frequency manipulation.
Completion detection circuits stall subsequent stages until valid DATA0/DATA1 emergence from NULL state.
Side-Channel Resistance
Balanced gate design minimizes power and timing variation across all input patterns.
Research demonstrates 130nm CMOS implementation with reduced side-channel leakage compared to dual-rail asynchronous designs.
Physical Security Assessment
Side-Channel Protection
Fault Injection Resistance
Implementation Status and Manufacturing Challenges
Research demonstrates DITL feasibility in 130nm CMOS, but manufacturing challenges remain for ternary encoding at scale. Standard binary CMOS optimization may introduce signal discrimination challenges between NULL and threshold-adjacent DATA states.
X. Dual-Lane Latency Architecture: Stress Test
Fast Lane
Sub-millisecond execution with local Merkle computation
Slow Lane
300-500ms anchoring with blockchain notarization
Critical Latency Window Exploitation
| Phase | Duration | Vulnerability | Detection Risk |
|---|---|---|---|
| Fast Lane Execution | <2ms | Action committed without evidentiary finality | High |
| Local Merkle Computation | ~10ms | Cryptographically valid but not externally notarized | Moderate |
| Blockchain Broadcast | 100-300ms | Mempool visibility without confirmation | Medium |
| Block Confirmation | 300-500ms | Finality achieved with consensus agreement | Low |
Exploit Vectors
Deferred Anchoring Failure
Fast Lane operates indefinitely without Slow Lane completion, creating permanent evidentiary gaps.
Merkle Manipulation
Root collision or selective inclusion/exclusion between local computation and broadcast.
Blockchain Front-running
Invalidating pending anchors through transaction ordering manipulation.
Mitigation Strategies
Shortened Batching Intervals
Reduces vulnerability window but increases operational cost proportionally.
Multiple Concurrent Anchors
Redundancy across multiple chains increases attack complexity and cost.
DITL-Gated Execution Interlock
Physical prevention of Fast Lane completion without Slow Lane initiation signal.
Critical Vulnerability: Deferred Anchoring Failure
The MAX(Lane 1, Lane 2) responsiveness rule creates semantic ambiguity where Fast Lane "completion" is defined as local Merkle root computation rather than external confirmation. This enables indefinite operation without genuine anchoring, fundamentally violating the No Log = No Action invariant.
XI. Supply Chain and Fabrication Risk
Foundry Compromise
Nation-state backdoors in DITL asynchronous circuits
Pre-Fabrication Tampering
Mask-level modification compromising physical layout
Post-Fabrication Modification
Field reprogramming or physical tampering after delivery
Multi-Vendor Redundancy vs. Standardization Tradeoff
Diversification Strategy
Security Benefits
Compromise of single vendor affects only fraction of deployment. Correlated failure risk reduced through heterogeneous implementations.
Verification Advantages
Cross-validation between different implementations enables detection of vendor-specific anomalies and backdoors.
Standardization Strategy
Economic Benefits
Volume production reduces per-unit cost. Standardized manufacturing processes improve yield and reliability.
Interoperability Gains
Uniform interface specifications simplify integration and enable consistent security analysis across deployment.
Global Fabrication System Challenge
Current global semiconductor fabrication systems optimized entirely for binary CMOS logic. Transition to DITL requires specialized processes with uncertain scale economics and potential concentration risk. Research demonstrates feasibility but manufacturing ecosystem development lags.
XII. Shadow System and Parallel Deployment Risk
Parallel Non-TL Architectures
Binary Inference Chips
High-performance accelerators bypassing TL governance constraints
Economic pressure creates demand for ungoverned computation, especially in high-frequency trading scenarios where Epistemic Hold delays create competitive disadvantage.
Cloud Forks without Anchoring
TL-governed algorithms deployed on non-compliant infrastructure
Supply chain compromise introduces TL-compliant algorithms into ungoverned execution environments, creating operational divergence while maintaining appearance of compliance.
Edge-Device Bypass Architectures
Resource-constrained endpoints with reduced Decision Log requirements
Performance optimization under resource constraints leads to gradual elimination of governance mechanisms, creating precedent for broader weakening.
Coordinated Shadow Execution Networks
Distributed Routing Networks
Systems routing around Hybrid Shield pseudonymization through coordinated network protocols that reassemble identity from distributed fragments.
Protocol-Level Evasion
Communication protocols designed to appear TL-compliant while enabling parallel ungoverned channels for sensitive information transfer.
Temporal Separation Attacks
Critical operations deferred to post-governance time windows, creating operational exceptions that become normalized precedents.
Minimum Adoption Threshold Analysis
| Protection Level | Adoption Threshold | Protection Mechanism | Shadow System Risk |
|---|---|---|---|
| Individual System | 100% | Local enforcement only | Critical |
| Institutional | 75-80% | Organizational policy enforcement | High |
| Industry Sector | 60-70% | Regulatory compliance framework | Moderate |
| Ecosystem-wide | 40-50% | Network effect and interoperability | Low |
System Coherence Requirements
Individual Protection Insufficient
Single-system TL protection ineffective against ecosystem-level adversarial pressure. Shadow systems provide alternative execution paths.
Institutional Coherence Required
Organizational-level adoption with policy enforcement creates meaningful protection but remains vulnerable to external competitive pressure.
Adversarial Adaptation
Shadow Network Formation
Adversaries coordinate distributed systems to route around TL governance, creating parallel execution networks with selective compliance.
Compliance Theater
Systems maintain appearance of TL compliance while enabling ungoverned execution through backdoors and exceptional circumstances.
Critical Challenge: Protection vs. Adoption Tradeoff
TL's comprehensive protection creates adoption friction through performance overhead and operational complexity. This friction creates incentives for shadow system development, suggesting that optimal security may require ecosystem-level coordination rather than individual system hardening.
XIII. Cryptographic Longevity and Quantum Threats
Hash Agility Strategy
SHA-256 to SHA-3 Migration Path
TL specification includes cryptographic agility with hash algorithm transition capability
Migration requires comprehensive re-anchoring of historical ledger with backward verification capability
Merkle Continuity Preservation
Chain of custody maintenance during algorithm transitions through nested Merkle proofs
Historical verification requires preservation of old hash algorithms with transition attestation
Key Compromise Containment
Ephemeral Key Rotation (EKR) mechanism with forward secrecy limiting compromise impact
EKR implementation complexity creates attack surface through epoch manipulation and heartbeat injection
Quantum Advantage Timeline
Shor's Algorithm Threat
Polynomial-time signature forgery enabling complete cryptographic collapse
Grover's Algorithm Impact
Square-root complexity reduction for hash preimage attacks
Post-Quantum Migration Path
Dilithium and SPHINCS+ integration with hybrid verification schemes
Temporal Resilience Assessment
Algorithm Migration Requirements
Timeline Risk Assessment
Short-term (0-5 years)
No immediate quantum threat, but preparation required for migration planning
Medium-term (5-15 years)
Grover's algorithm impact requires hash function migration and Merkle reconstruction
Long-term (15-30 years)
Shor's algorithm threat requires complete cryptographic ecosystem replacement
Blockchain Collapse Scenario
Beyond quantum threats, TL faces systemic risk from blockchain platform collapse through 51% attacks, de-platforming, or quantum advantage. Multi-chain anchoring provides resilience against single-chain failure, but coordinated multi-chain attacks maintain systemic vulnerability requiring broader ecosystem diversification.
XIV. Economic and Political Pressure
Regulatory Hostility Scenarios
Central Bank Resistance
Opposition to immutable monetary policy logging creating transparency conflicts
Central banks may resist TL implementation for CBDC systems where immutable logging conflicts with monetary policy flexibility requirements.
Export Control Restrictions
DITL chip restrictions and technology transfer limitations
State-level controls on advanced cryptography and hardware security technologies may limit DITL availability and create supply chain vulnerabilities.
Lawful Interception Mandates
Mandatory backdoors and identity revelation requirements
Legal coercion for identity revelation and transaction monitoring may conflict with TL's pseudonymization and privacy protection principles.
Profit-Driven Weakening Pressure
Shareholder Pressure
Economic demand to disable "inefficient" Epistemic Hold delays creates market selection pressure against constitutional compliance.
Competitive Disadvantage
Competitors without TL constraints gain temporary advantage through reduced operational overhead and faster execution cycles.
Market Selection Effects
Short-term market pressures favor systems optimizing for speed over caution, creating evolutionary disadvantage for prudential architectures.
Adoption Scenario Modeling
| Adoption Scenario | Driver | Security Outcome | Probability |
|---|---|---|---|
| Public Adoption | Transparent, certified deployment | Strongest protection with ecosystem coordination | High |
| Quiet Institutional | Competitive advantage via trusted execution | Strong protection but limited scope | Moderate |
| Mandatory Adoption | CBDC or SIFI regulatory mandate | Strongest protection with enforcement infrastructure | Low |
| Partial Adoption | Mixed compliance with TL and non-TL systems | Weakened protection through shadow systems | High |
Macro-Coercion Scenarios
State-Level Coercion
Mandated backdoors and lawful interception requirements may conflict with TL's constitutional principles, requiring organizational resistance with potential legal consequences.
Economic Sanctions
Export controls and technology transfer restrictions may limit DITL availability and create supply chain vulnerabilities requiring geopolitical diversification.
Market Dynamics
Network Effect Protection
Ecosystem-wide adoption creates protection through interoperability requirements and collective governance reinforcement.
First-Mover Advantage
Early adopters gain competitive advantage through trusted execution, creating market incentives for broader adoption.
Balancing Security and Adoption
TL's comprehensive protection creates adoption friction through performance overhead and operational complexity. Optimal security may require ecosystem-level coordination rather than individual system hardening, suggesting that governance architecture must balance constitutional rigor with practical adoption constraints.
Final Verdict
Enforceable Under Hostile Control
With DITL hardware realization, TL provides meaningful constitutional constraint against administrative override and software-mediated attacks.
Partially Enforceable Under Contested Hardware
Physical access and fault injection attacks create residual vulnerability even with DITL realization, requiring additional tamper-responsive protections.
Non-Enforceable Under Inconvenient Truth
When truth becomes organizationally inconvenient, economic and political pressure creates irresistible demand for override mechanisms.
Collapse Threshold Assessment
TL meets the collapse threshold definition through two Critical-rated pillars (Epistemic Hold, Goukassian Principle) whose individual compromise constitutes system failure. Additionally, software-only deployments satisfy condition (c) of the collapse threshold, rendering TL non-enforceable in emulation mode.
Critical Dependencies
Residual Vulnerabilities
Recommendation: TL provides meaningful constitutional constraint when implemented with DITL hardware, but requires continued governance vigilance and ecosystem coordination to maintain integrity against adversarial pressure and implementation challenges.