No Log = No Action
Execution Integrity Specification
A hardware-enforced architectural constraint that makes log commitment a strict prerequisite for all execution release in Ternary Logic systems, eliminating the evidentiary debt of traditional asynchronous telemetry through cryptographic coupling and physical existence gating.
I. Problem Definition: Optional Logging Failure
I.1 Asynchronous Telemetry and Non-Determinism
Audio Briefing — No Log = No Action
A 5:43-minute overview of the execution integrity invariant: cryptographic enforcement, Epistemic Hold, and the dual-lane commitment architecture.
Traditional computing systems fundamentally rely upon asynchronous telemetry mechanisms for observability, creating an inherent architectural decoupling between the execution of operations and the persistence of their corresponding audit records. This decoupling manifests as a temporal gap between the moment an action completes and the moment its corresponding log entry becomes durable, during which any number of failure modes may intervene to prevent successful persistence.
The silent nature of these failures is particularly pernicious: the absence of a log entry cannot be distinguished from the absence of an action without independent verification mechanisms that the architecture itself fails to provide. This creates a false sense of completeness that is more dangerous than acknowledged absence, as investigators may proceed with confidence in their analysis while remaining unaware of the missing evidence.
I.2 Post-Hoc Reconstruction Limitations
The limitations of post-hoc reconstruction become apparent when systems attempt to establish behavioral provenance from incomplete or inconsistent log data. When log entries are missing due to buffer overflow, network congestion, or storage exhaustion, reconstruction algorithms must operate upon an incomplete evidentiary substrate, producing outputs that may be technically consistent with available data yet factually incorrect regarding actual system behavior.
Evidence Gaps
Missing entries are fundamentally unbridgeable: no algorithm can recover information that was never recorded.
Adversarial Amplification
Attackers can deliberately trigger conditions that cause log loss while executing malicious actions.
I.3 Bypass Vectors in Emergency and Hardware Paths
Emergency shutdown sequences in traditional systems frequently implement direct hardware manipulation paths that circumvent normal software logging stacks. These sequences, designed for rapid response to critical conditions, prioritize speed over comprehensiveness, with hard-coded paths that write directly to hardware registers or trigger physical mechanisms without software mediation.
II. The Invariant: "No Log = No Action"
II.1 Formal Predicate Logic Definition
The "No Log = No Action" invariant is formally defined as a universal constraint over all possible system executions. Let A denote the set of all actions, where each action a ∈ A represents a potential state transition, transaction, or physical actuation. Let L denote the set of all log entries, with l_a ∈ L representing the entry corresponding to action a.
II.2 Linear Temporal Logic Specification
The temporal dynamics are formally specified using Linear Temporal Logic (LTL) with strict Until operator semantics, capturing the requirement that log commitment must precede action release in all possible execution traces.
II.3 Log Completeness Criteria
Canonical Serialization
Deterministic byte sequence with explicit field ordering, fixed-width encoding, and versioned format.
Cryptographic Hashing
Preimage-resistant, collision-resistant integrity anchor computed in hardware-protected environments.
Physical Persistence
Read-back confirmation from non-volatile accumulator with write atomicity and remanence resistance.
II.4 Action Definition and Scope
The action definition comprehensively encompasses all mechanisms by which a system produces effects upon its environment. This includes externally observable effects such as API responses and network transmissions; persistent state mutations including database writes and configuration changes; and cyber-physical boundary actuations comprising motor commands, valve positions, and energy conversion to the physical environment.
III. Cryptographic Actuator Interlock and Execution Coupling
III.1 Protocol-Level Execution Gating
The transformation of logging from observability mechanism to protocol-level execution gate represents the central architectural innovation. The write-before-release model embeds this participation directly into the execution path, such that the attempt to release an action necessarily traverses the logging verification logic, with no alternative pathway that could circumvent this traversal.
III.2 Hardware-Protected Register Architecture
The registers maintaining the Merkle accumulator root are implemented as hardware-protected structures with access controls that enforce logging-subsystem exclusivity. These registers are readable by the execution gating logic for verification purposes but modifiable only by the logging subsystem's hardware state machines, with no processor instruction, DMA transfer, or debug interface capable of direct modification.
III.3 Triple Cryptographic Requirements for Release
Hash Verification
Preimage-resistant log hash validation with structural verification and collision resistance.
Attestation Quote
Hardware-generated proof of physical persistence with TPM-signed evidence and platform state attestation.
Inference Containment
Information flow control preventing result propagation until logging completes with side-channel countermeasures.
III.4 Non-Bypassability Guarantees
The architectural design explicitly excludes administrative privilege as a mechanism for bypassing execution gating. Traditional superuser or root privileges that enable unrestricted system access do not extend to the capability token registers or the execution release gate. This exclusion is implemented through hardware access controls that are not subject to software configuration, with physical isolation preventing any software-privileged operation from affecting the gate state.
III.5 Transactional Commit Semantics
The logging and execution operations are structured as a distributed transaction with atomic commit semantics, ensuring that partial failures cannot result in states where logging is incomplete yet action has occurred, or where logging is complete yet action fails to occur. The transaction scope encompasses log entry generation, hash computation, accumulator update, physical persistence, capability token issuance, and action release signal generation.
IV. Hardware Root of Trust
IV.1 Secure Enclave Integration
Secure enclaves provide isolated execution environments where the logging subsystem and execution gate logic operate with protection from observation and modification by software outside the enclave boundary. The enclave boundary encompasses the processors, memory, and hardware accelerators dedicated to log processing, with cryptographic mechanisms ensuring that code and data within the enclave cannot be accessed by software outside.
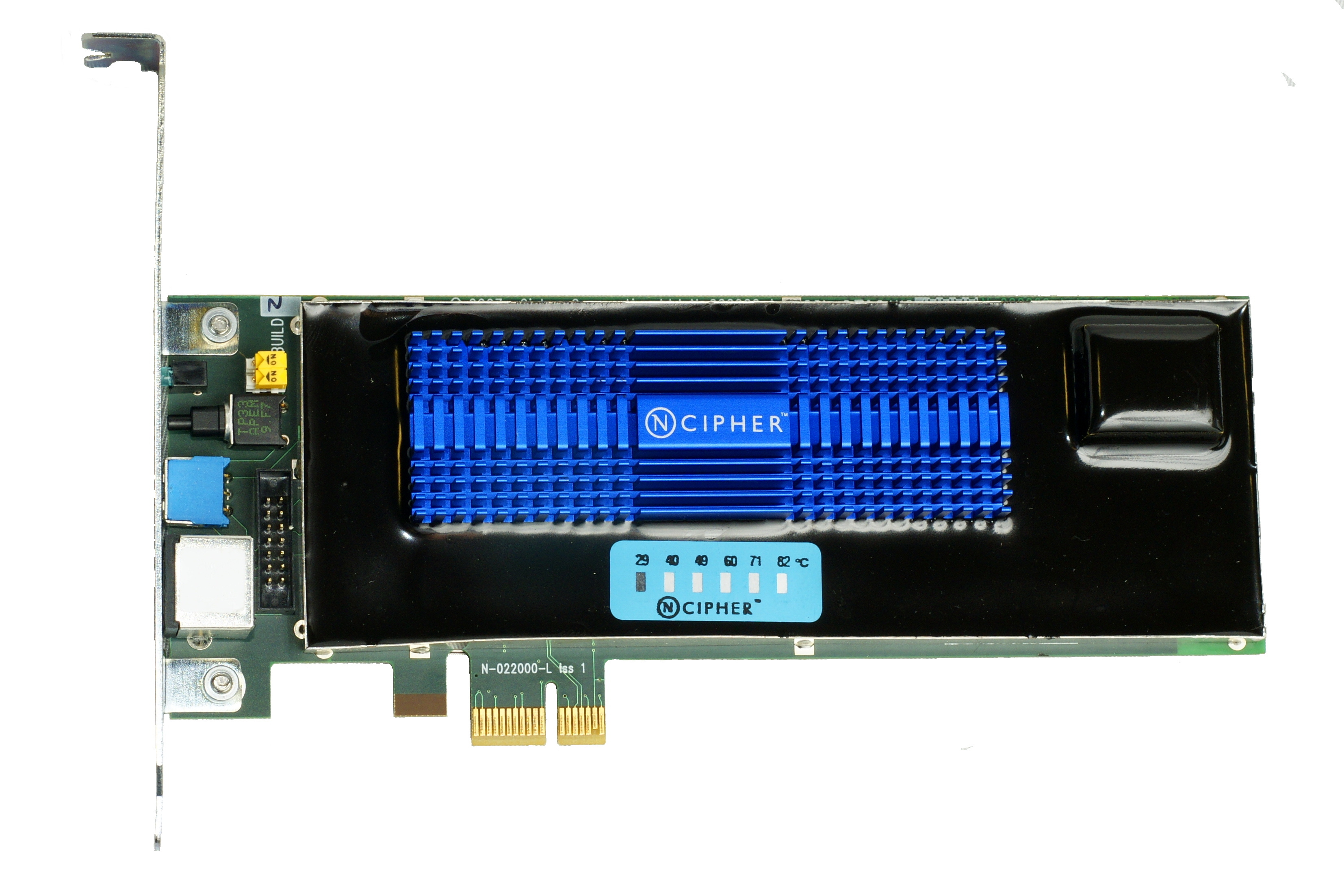
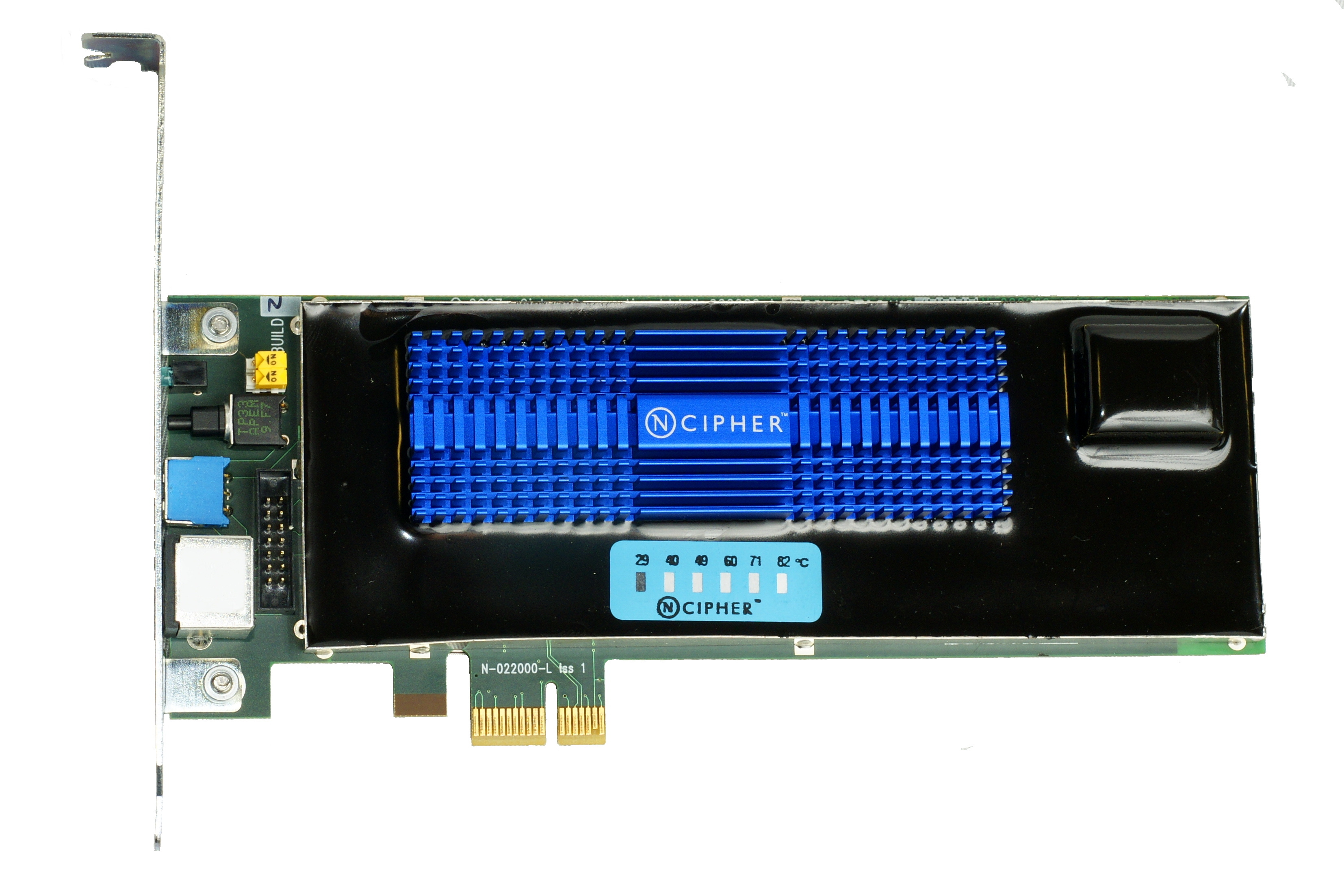
Hardware security module with tamper detection mechanisms for physical security assurance
IV.2 Trusted Platform Module Functions
The Trusted Platform Module (TPM) provides foundational capabilities for platform integrity measurement and reporting. Platform integrity measurement captures the state of system software from boot ROM through firmware to operating system in a chain of hash computations extended into TPM Platform Configuration Registers (PCRs).
Integrity Measurement
Chain of hash computations from boot ROM to operating system, capturing the complete software stack state.
Secure Storage
Non-exportable key storage with hardware random number generation and authorization policies.
Attestation Quotes
Hardware-generated evidence of platform state and log commitment with replay protection.
IV.3 Hardware Security Module Backing
For deployments requiring higher assurance than commodity TPMs provide, dedicated Hardware Security Modules (HSMs) offer FIPS 140-2 or FIPS 140-3 certified implementations with rigorous physical and logical security controls. HSMs provide higher-grade tamper resistance with active shielding, environmental sensors, and key destruction upon detected intrusion.
IV.4 Full Trust Chain Construction
Physical Unclonable Functions (PUFs) bind cryptographic keys to specific silicon instances through manufacturing variation that is uncontrollable, unpredictable, and unclonable. PUF-based key derivation ensures that extracted keys from one device are useless for impersonating another, preventing device substitution attacks.
IV.5 Software-Only Enforcement Insufficiency
Kernel compromise demonstrates the fundamental inadequacy of software-only enforcement. A compromised kernel can modify system call tables to intercept and suppress logging calls, directly manipulate log files, forge timestamps, and present false information to remote verification systems. The hardware-based gate is immune to kernel compromise because its operation does not depend on kernel-controlled resources.
V. Ternary Logic Mapping and Epistemic Hold / Solvency Protocol
V.1 Triadic Decision Space Definition
Act State (+1)
Committed execution with confidence thresholds satisfied, inputs consistent and complete, all preconditions verified.
Refuse State (-1)
Definitive rejection due to policy violations, risk assessment results, or constraint exceedances with full rationale documentation.
Epistemic Hold (0)
Suspended deliberation when confidence is insufficient for reliable classification, preserving optionality while preventing premature commitment.
V.2 Solvency Protocol in Financial Contexts
In financial and economic decision-making contexts, the Epistemic Hold state implements the Solvency Protocol that preserves system integrity through transaction halting when confidence conditions are not satisfied. The protocol recognizes that financial actions, once executed, may create irreversible obligations, position changes, or counterparty exposures that constrain subsequent options and potentially propagate instability through interconnected networks.
Transaction Execution"] B -->|"≤1%"| D["Refuse State
Transaction Rejection"] B -->|"1-99%"| E["Epistemic Hold
Solvency Protocol"] E --> F["Liquidity Preservation"] F --> G["Position Freezing"] G --> H["Transaction Halt"] H --> I["Mandatory Escalation"] C --> J["Logged Execution"] D --> K["Logged Rejection"] E --> L["Logged Suspension"] style A fill:#e3f2fd style B fill:#fff3e0 style C fill:#c8e6c9 style D fill:#ffcdd2 style E fill:#fff9c4 style J fill:#e8f5e8 style K fill:#ffebee style L fill:#fffde7
V.3 Epistemic Hold Trigger Conditions
Insufficient Confidence Metrics
Calculated confidence in decision outcomes falls below configured thresholds due to model uncertainty, input quality degradation, or out-of-distribution conditions.
Conflicting Input Detection
Multiple information sources provide mutually inconsistent data that cannot be reconciled through standard fusion methods.
Incomplete Data States
Required information is missing, delayed beyond timeout thresholds, or fails quality checks that would enable reliable use.
Outlier Detection Beyond Validated Envelopes
Statistical process control and machine learning techniques identify inputs that deviate significantly from historical patterns or model predictions.
VI. Cryptographic Non-Repudiation of Action
Verifiable prior log requirements establish that every action is cryptographically linked to predecessor log entries, creating chains of proof from system initialization through current states. Merkle proof techniques provide logarithmic-size evidence of inclusion and ordering, enabling third-party verification independent of continued operator cooperation.
Digital Signature Binding
Actor identity binding to action commitments ensures authorizing parties cannot repudiate involvement, with signatures computed over action content and documentary precedent.
Complete Trace Reconstruction
Logs serve as behavioral proof enabling complete trace reconstruction with third-party verification through Merkle inclusion proofs and hardware attestation.
Invalid Execution States and Response
Orphaned Actions
Actions without corresponding log entries trigger immediate safe harbor transition with key rotation and log segment quarantine.
Hash Mismatches
Tampering detection through hash verification failures results in immediate system halt and forensic preservation of state.
Signature Verification Failures
Authentication failures trigger credential revocation, access control revalidation, and comprehensive security audit.
VII. Cryptographic Primitives and Adversarial Resistance
VII.1 Canonicalization and Representation Elimination
Canonicalization eliminates representation ambiguity through deterministic serialization with explicit byte-level field ordering and encoding standards. Length-prefixed encoding replaces delimiter-based termination, normalized string representations ensure consistent text processing, and version negotiation enables format evolution while maintaining backward verifiability.
The canonicalization protocol executes within the trusted computing base, with serialized output being the direct input to cryptographic hashing, preventing manipulation between serialization and integrity protection.
VII.2 Append-Only Structures and Tamper Evidence
Hash chains and Merkle accumulators ensure tamper evidence with avalanche sensitivity to single-bit modification propagating through entire subsequent chains. The append-only nature prevents undetectable deletion or modification, while periodic cross-anchoring to external timestamp services provides additional protection against rollback attacks.
VII.3 Replay Protection and Logging Suppression
Timestamp Granularity
Hardware-protected clocks with granularity exceeding action execution rates, synchronized through protocols with bounded uncertainty.
Redundant Channels
Byzantine fault tolerant redundant logging channels with covert channel detection and suppression countermeasures.
VII.4 Insider Threat Mitigation and Silent Action Prevention
Multi-party authorization for administrative functions with separation of duties between logging and action authorization prevents single-point compromise. Behavioral anomaly detection monitors privileged user activities, while observable energy consumption correlation with logged activity provides external monitoring independence.
VIII. Failure Modes and Cyber-Physical / Financial Safe Harbor States
VIII.1 Fail-Closed Behavior Across Critical Failure Modes
Storage Failures
- • Storage medium write failures
- • Read-back verification inconsistencies
- • Accumulator overflow conditions
- • Memory corruption detection
Cryptographic Failures
- • Hashing inconsistency detection
- • Signature verification failures
- • Key rotation failures
- • Certificate expiration
VIII.2 Cyber-Physical Safe Harbor Definition
For cyber-physical systems, safe harbor states are defined by kinetic energy minimization with bounded convergence time, controlled deceleration with bounded jerk and acceleration profiles, and stable equilibrium achievement without active control. The transition dynamics are pre-computed and verified to achieve safe state from all operational conditions.
The separation between high-level decision authority denial and low-level control stability preservation is maintained through stabilizing controllers independent of decision authority and safety envelope constraints enforced through separate hardware pathways.
VIII.3 Financial Safe Harbor Definition
For financial or data-driven implementations, the safe harbor state is defined as immediate transaction halting and liquidity preservation, running parallel to the kinetic safe harbors of cyber-physical systems. This ensures the specification addresses both domains without conflation, with liquidity preservation protocols preventing new obligation creation while maintaining asset availability.
Cyber-Physical Safe Harbor
- • Kinetic energy minimization
- • Bounded convergence time
- • Controlled deceleration profiles
- • Passive stability achievement
Financial Safe Harbor
- • Immediate transaction halting
- • Liquidity preservation
- • Obligation prevention
- • Asset availability maintenance
VIII.4 State Machines with Model-Checked Transitions
State machines with model-checked transitions ensure all mode changes lead to safe states, with formal verification of transition correctness and completeness. Passive hazard analysis demonstrates why passive states are insufficient for momentum-carrying or thermally active systems, requiring active control to safe conditions.
VIII.5 Manual Override Procedures
Manual override procedures require physical presence and multi-party authorization subject to complete logging and subsequent audit. Override attempts are themselves logged through dedicated emergency paths, with the fact of override and its justification captured for post-incident analysis.

Physical emergency stop system requiring multi-party authorization and comprehensive logging
IX. Integration with Dual-Lane Architecture
IX.1 Fast Lane: Local Hardware-Backed Commitment
The fast lane enables local hardware-backed commitment within a strict sub-two-millisecond latency bound, implemented through dedicated hardware pipelines in FPGA or ASIC technology with simplified log entry formats and battery-backed non-volatile accumulators sufficient for action release. This lane provides the performance required for high-frequency execution while maintaining the invariant's safety guarantees.
Performance Characteristics
- • Sub-2ms latency guarantee
- • Dedicated hardware pipelines
- • Simplified log entry formats
- • Battery-backed NV memory
Security Guarantees
- • Hardware-backed persistence
- • Cryptographic commitment
- • Non-bypassable gating
- • Immediate verification
IX.2 Slow Lane: Asynchronous External Anchoring
The slow lane provides asynchronous anchoring to distributed ledgers or timestamp services for external auditability, with batch compression and cryptographic aggregation preserving individual entry verifiability via Merkle inclusion proofs. This lane enables long-term evidentiary preservation and third-party verification without impacting real-time performance.
Important Clarification: Delayed anchoring does not violate the invariant because execution depends exclusively on guaranteed local physical commitment, not immediate global publication. Slow lane failures do not block continued fast lane operation.
IX.3 Backpressure and Circuit Breaker Behaviors
Backpressure and circuit breaker behaviors manage the interaction between fast and slow lanes, with fast lane queue depth monitoring and admission control preventing overload. Slow lane backlogs trigger rate limiting or batch size increases, while lane isolation prevents cascading failures across boundaries.
Sub-2ms Commit"] B -->|"Reject"| D["Queue/Backoff"] C --> E["Local Hardware Commit"] E --> F["Slow Lane Queue"] F --> G{"Slow Lane Status"} G -->|"Healthy"| H["Batch & Anchor
External Verification"] G -->|"Backlog"| I["Rate Limiting
Circuit Breaker"] H --> J["Distributed Ledger
Timestamp Service"] I --> K["Queue Management
Admission Control"] C --> L["Immediate Response"] J --> M["Long-term Evidence"] K --> N["System Stability"] style A fill:#e3f2fd style C fill:#e8f5e8 style E fill:#fff3e0 style H fill:#e1f5fe style I fill:#fff9c4 style J fill:#f3e5f5 style L fill:#c8e6c9 style M fill:#f3e5f5 style N fill:#fffde7 style B fill:#fff3e0 style G fill:#fff3e0
IX.4 Gap Tolerance and Safety-Critical Constraints
The gap tolerance bound is defined by safety-critical time constants ensuring slow lane delays do not create hazardous uncertainty windows. The system maintains operational safety even with extended slow lane propagation times, as the fast lane's hardware-backed commitment provides immediate safety guarantees independent of external verification timing.