
Authentication Failure Analysis
Under Politically Sensitive Load Surge Conditions
A forensic investigation into Anthropic's authentication outage during unprecedented demand surge and supply chain risk designation
Key Finding
70% confidence in internal architectural fragility exposed by scale, particularly recent OAuth infrastructure changes. Hybrid DDoS remains technically plausible (15% confidence) but lacks evidentiary support.
Executive Summary
March 2, 2026: Anthropic's Claude AI platform experienced a ~5-hour authentication outage while core API services remained operational, coinciding with unprecedented political and user surge pressures.
Forensic analysis cannot conclusively determine causation: the outage pattern aligns most closely with internal architectural fragility exposed by scale, though hybrid DDoS concealed within legitimate surge remains technically plausible.
Incident Overview
On March 2, 2026, Anthropic's Claude AI platform experienced a significant authentication infrastructure failure at 11:49 UTC, rendering web and mobile interfaces inaccessible while paradoxically preserving core API functionality. The incident persisted for approximately five hours, with substantial service restoration achieved by 16:00–17:00 UTC.
The outage occurred merely 72 hours after President Trump directed federal agencies to cease Anthropic technology usage, and Defense Secretary Pete Hegseth designated the company a "supply chain risk to national security". Simultaneously, Claude had achieved #1 ranking on Apple's U.S. App Store, driven by user migration from competitors.
Classification of Outage Causation
Most Likely (70% confidence)
Internal Architectural Fragility
Recent OAuth infrastructure changes, API/web segregation pattern
Contributing (55% confidence)
Organic Surge Failure
App Store #1 ranking, unprecedented demand characterization
Plausible (15% confidence)
Opportunistic Attack
Political timing, demonstrated actor capabilities
Unlikely (10% confidence)
Pure Volumetric DDoS
API preservation contradicts network-layer attack pattern
Timeline Reconstruction
Pre-Incident Context (February 27–March 1, 2026)
February 27: Pentagon Dispute Escalation
Defense Secretary Pete Hegseth imposed a 5:01 p.m. deadline for Anthropic to remove safeguards restricting military use. Anthropic's refusal triggered:
- Presidential directive to cease all federal agency usage
- "Supply chain risk to national security" designation
- CEO Dario Amodei's public confrontation statement
March 1: User Migration Patterns
Instructional content for migrating from ChatGPT to Claude achieved significant distribution, driven by protest against competitor platforms' Pentagon partnerships. Claude reached #1 on Apple's U.S. App Store.
Incident Chronology (March 2, 2026 UTC)
11:49 UTC - Initial Error Detection
T+0 minAnthropic status page: "Elevated errors on claude.ai, console, and claude code." DownDetector shows surge in user reports starting ~12:00 UTC.
12:21 UTC - API Segregation Identified
T+32 minCritical forensic evidence: "Claude API working as intended. Issues related to Claude.ai and login/logout paths."
13:22 UTC - Root Cause Identified
T+93 min"Issue identified and fix being implemented." No root cause disclosed.
15:50 UTC - Service Restoration
T+4h 1mFull functionality returning gradually. Total duration: ~5 hours.
Post-Incident Pattern: April 2 Recurrence
April 2, 2026 - Failed Fix Implementation
Users "again reported errors" with HTTP 529 error codes. Anthropic "attempted to implement a fix, but it failed."
Significance: Failed fix implementation suggests incomplete root cause identification or persistent architectural fragility.
Authentication Plane Architecture Modeling
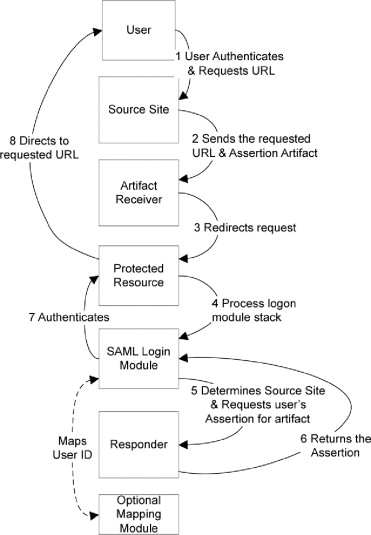
Standard SaaS Authentication Stack
- Login Endpoints: claude.ai/login with session management
- OAuth Infrastructure: ANTHROPIC_AUTH_TOKEN deployment Feb 28
- Database & Cache: User credentials, session store, rate limiting
- WAF & Rate Limiting: Traffic classification and security controls
Recent Architectural Changes
February 28, 2026
OAuth Support Deployment: ANTHROPIC_AUTH_TOKEN environment variable for Claude Code authentication
- 48-hour pre-incident window
- New authentication code path introduction
- External identity provider dependency
Structural Choke Points Under Surge
Connection Pool Exhaustion
Database Saturation Cascade
API/Web Interface Segregation Evidence
Critical Diagnostic Evidence: API preservation while web interface failed suggests architectural separation between authentication mechanisms.
Possible Explanations
- • Separate authentication domains (API keys vs. sessions)
- • Different scaling limits and traffic patterns
- • Infrastructure isolation with failure domain boundaries
- • Deliberate API prioritization during degradation
Confidence Assessment
Hybrid DDoS Plausibility Assessment
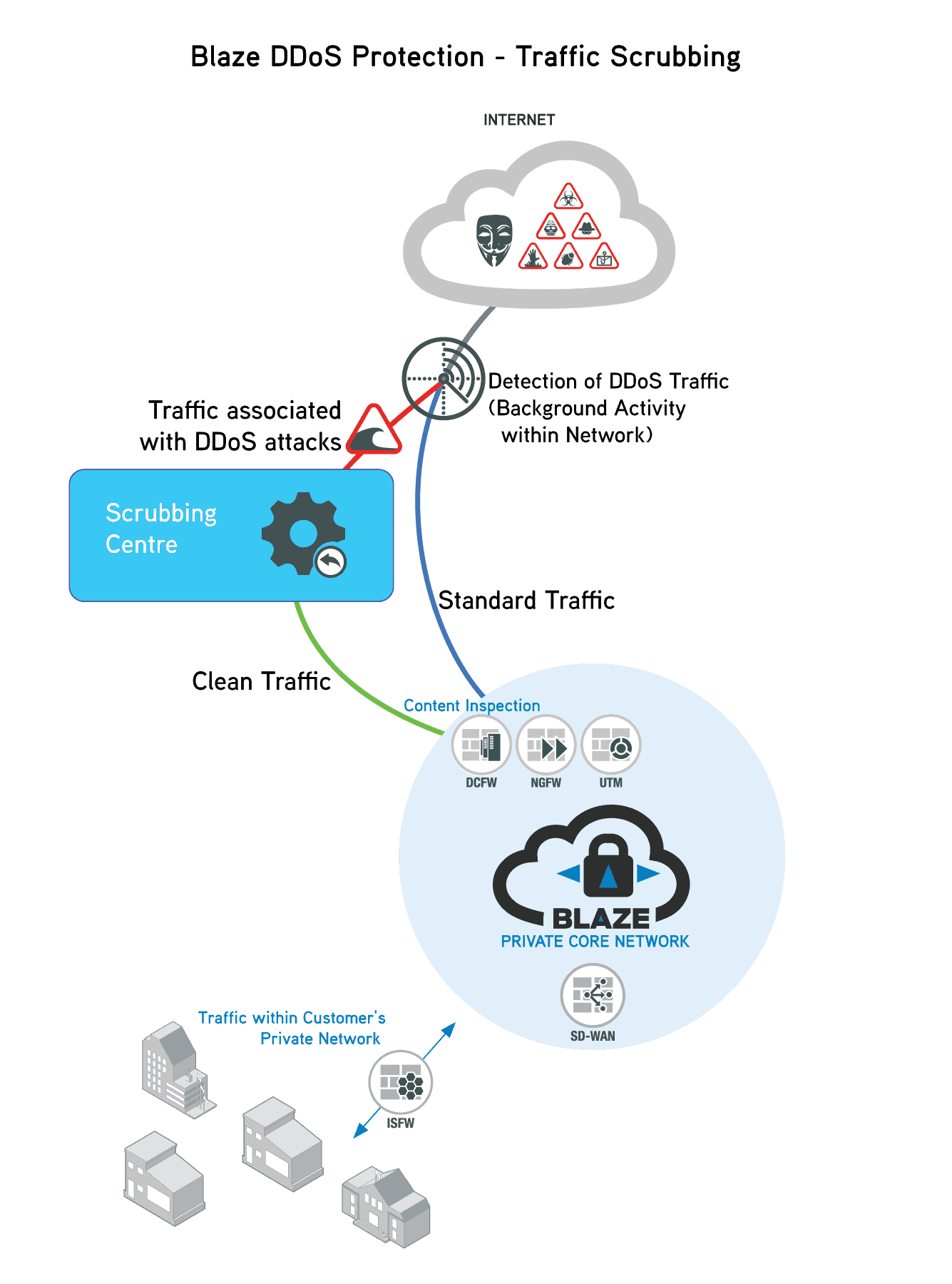
Attack Vector Taxonomy
Behavioral Signature Analysis
Required Forensic Artifacts
Critical Gap: No behavioral data published prevents distinguishing organic surge from coordinated attack.
Capability Precedent: GTG-1002 Incident
November 2025: Anthropic disclosed disruption of the first reported AI-orchestrated cyber espionage campaign, where Chinese state-sponsored actors used Claude Code to automate 80–90% of cyber espionage tasks.
Demonstrated Capabilities
- • Reconnaissance and vulnerability discovery
- • Exploitation and payload generation
- • Data exfiltration automation
- • Campaign orchestration with AI assistance
Relevance Assessment
Plausibility Conclusion
Political Timing Correlation Analysis

Pentagon Negotiation Breakdown
Public Response & User Migration
Comparative Case Analysis
| Platform | Date | Political Context | Classification |
|---|---|---|---|
| OpenAI | Nov 2023 | Israel-Gaza conflict positioning | Ambiguous |
| Cloudflare | Nov 2025 | Content moderation controversies | Infrastructure |
| Anthropic | Mar 2026 | Pentagon dispute, supply chain risk | Architectural Fragility |
Concurrent Global Cyber Activity
March 2, 2026: Same day as Anthropic outage, significant cyber activity in Middle East following Israeli-US strikes on Iran.
Incident Response Evaluation
Response Timeline
Service Preservation
Transparency
Communication Timeline Analysis
Transparency Gaps
- • No technical root cause disclosure
- • No error rate quantification
- • No affected user percentage
- • No geographic scope details
- • No traffic volume metrics
- • No WAF or security alerts
Service Segregation Success
- • API functionality preserved throughout
- • Clear architectural boundaries maintained
- • Critical infrastructure prioritized
- • Demonstrates failure domain isolation
- • Enables differential degradation strategy
April 2 Recurrence Analysis
One month later, similar outage occurred with HTTP 529 errors and explicitly failed fix implementation.
Implications
- • Incomplete root cause understanding
- • Persistent architectural fragility
- • Distinct but related failure mode
Concerns
- • Recurrence pattern indicates systematic issue
- • Failed fix suggests complexity underestimation
- • Architectural redesign may be necessary
Governance Comparison: Ternary Moral Logic Framework
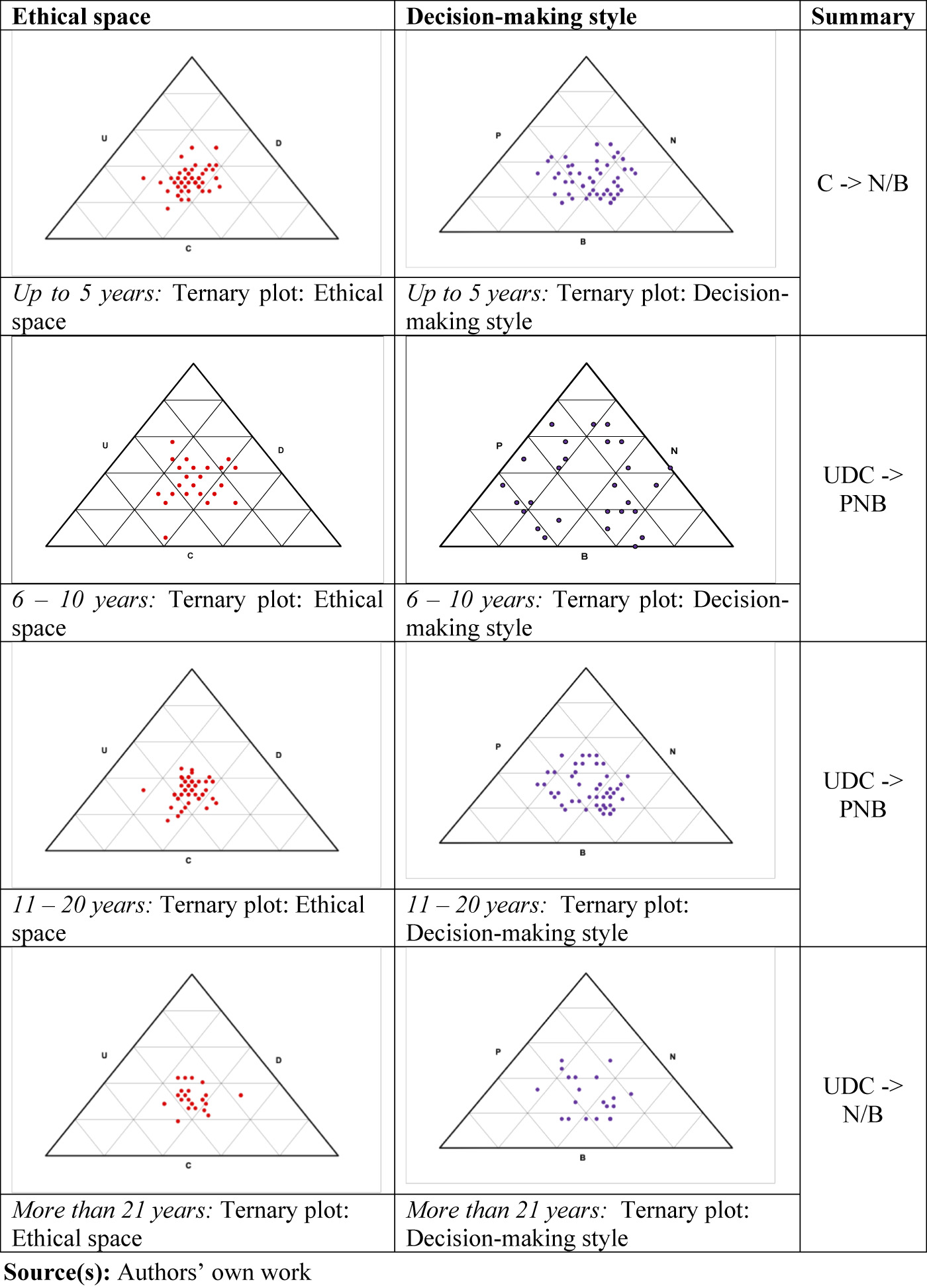
Binary Fail-Closed Limitations
Ternary Moral Logic Advantages
TML Architectural Mechanisms
Sacred Zero Trigger on Anomaly Detection
Parallel Moral Audit Thread
- • Rapid mitigation
- • Service preservation
- • Prevents evidence corruption
- • Evidence collection
- • Attribution analysis
- • Uncertainty quantification
Immutable Merkle-Based Incident Logging
Hypothetical TML Response Simulation
| Phase | Actual Response | TML Response |
|---|---|---|
| Detection | "Elevated errors" | Sacred Zero trigger; signed status with uncertainty preservation |
| Investigation | Opaque, no visibility | Parallel moral audit reporting; challenge mode for uncertain cohorts |
| Segregation ID | Implicit API survival | Explicit ethical mode fallback announcement |
| Restoration | Gradual recovery | Verifiable restoration with uncertainty tracking |
| Post-incident | No detailed disclosure | Merkle-anchored log publication; 72-hour transparency commitment |
Strategic and Architectural Recommendations
Authentication Plane Isolation
- Dedicated auth service boundaries with independent scaling
- Failure domain segregation and blast radius containment
- Resource isolation with CPU/memory quotas
Progressive Challenge Systems
- Adaptive rate limiting with behavioral signals
- Proof-of-work or CAPTCHA escalation pathways
- Reputation scoring and resource cost tracking
Telemetry Preservation Standards
- Immutable logging with 90-day minimum retention
- Real-time anomaly detection with ML integration
- Cross-organization attestation for CDN analytics
Merkle-Anchored Incident Logging
- Cryptographic verification of status communications
- Third-party auditability with community verification
- Daily Merkle tree root publication
Implementation Priority Matrix
| Recommendation | Impact | Effort | Priority |
|---|---|---|---|
| Authentication plane isolation | High | Medium | P0 |
| Immutable logging requirements | High | Low | P0 |
| Progressive challenge systems | High | Medium | P1 |
| Merkle-anchored logging | Medium | High | P1 |
| Surge simulation testing | High | High | P2 |
Politically Charged Scenario Modeling
Solidarity Migration Scenario
Hybrid Attack Scenario
Evidentiary Integrity Requirements
Future incidents require comprehensive forensic data collection to enable definitive attribution and root cause analysis.
P0 Artifacts (Critical)
- • Raw authentication logs (90-day retention)
- • WAF telemetry with request samples (30-day retention)
- • Database performance metrics (sub-second granularity)
P1 Artifacts (Important)
- • CDN edge analytics (7-day retention)
- • Network flow records (24-hour operational)
- • ASN distribution with temporal granularity