No Log = No Action:
Ternary Moral Logic Enforcement Specification
A binding architectural constraint that cryptographically couples execution to memory, transforming transparency from passive property to active system enforcement.
Executive Summary
Cryptographic Binding
Execution is cryptographically coupled to memory through hardware-enforced gates, making transparency an active system constraint.
Fail-Closed Design
All failure modes default to execution denial, with safe harbor states ensuring physical safety during logging failures.
Sub-2ms Latency
Dual-lane architecture achieves sub-2ms commitment latency while maintaining global verifiability through asynchronous anchoring.
I. Problem Definition: Optional Logging Failure
Traditional logging architectures suffer from a fundamental structural defect that renders them unsuitable for accountability-critical autonomous systems: they operate as asynchronous background processes decoupled from the execution paths they purport to document. The resulting temporal gap between action occurrence and log commitment—typically milliseconds to seconds under normal operation, unbounded under stress—admits catastrophic loss scenarios where system crashes, power failures, or resource exhaustion obliterate documentary traces of completed actions.
Telemetry-based accountability mechanisms compound these deficiencies through network-dependent delivery semantics. Network partitions, whether from infrastructure degradation, adversarial interference, or mobility-induced connectivity transitions, sever the path between event generation and log aggregation without guaranteed notification to the originating system. The Network Time Protocol, ubiquitous despite known limitations, typically achieves accuracy measured in tens of milliseconds—an eternity in processor cycles where critical decisions execute in nanoseconds.
Emergency shutdown sequences, designed for rapid system termination under hazard conditions, frequently bypass standard logging infrastructure to achieve deterministic latency targets, creating precisely the high-stakes scenarios where accountability is most critical but least available. Direct hardware manipulation through memory-mapped I/O, DMA engines, or JTAG debug interfaces permits actuation commands to reach physical interfaces without traversing software stacks including their logging instrumentation.
Post-hoc reconstruction techniques attempt to recover accountability through state inference, physical simulation, and witness testimony, but these methods prove fundamentally insufficient for high-consequence autonomous operation. Missing state vectors—including internal neural network activations, entropy source outputs, and precise sensor calibration parameters—prevent deterministic replay even when external behavior is approximately known.
II. The Invariant: "No Log = No Action"
The transformation from conventional optional logging to mandatory invariant enforcement requires formal specification as a system property holding across all execution paths without exception. The predicate logic formulation captures this as: for all execution paths P and actions a in the action set A, Executed(a) → ∃l ∈ L : Logged(l) ∧ Precedes(l, a) ∧ Verifiable(l), where L denotes committed log entries, Precedes establishes strict temporal ordering, and Verifiable denotes cryptographic integrity satisfaction.
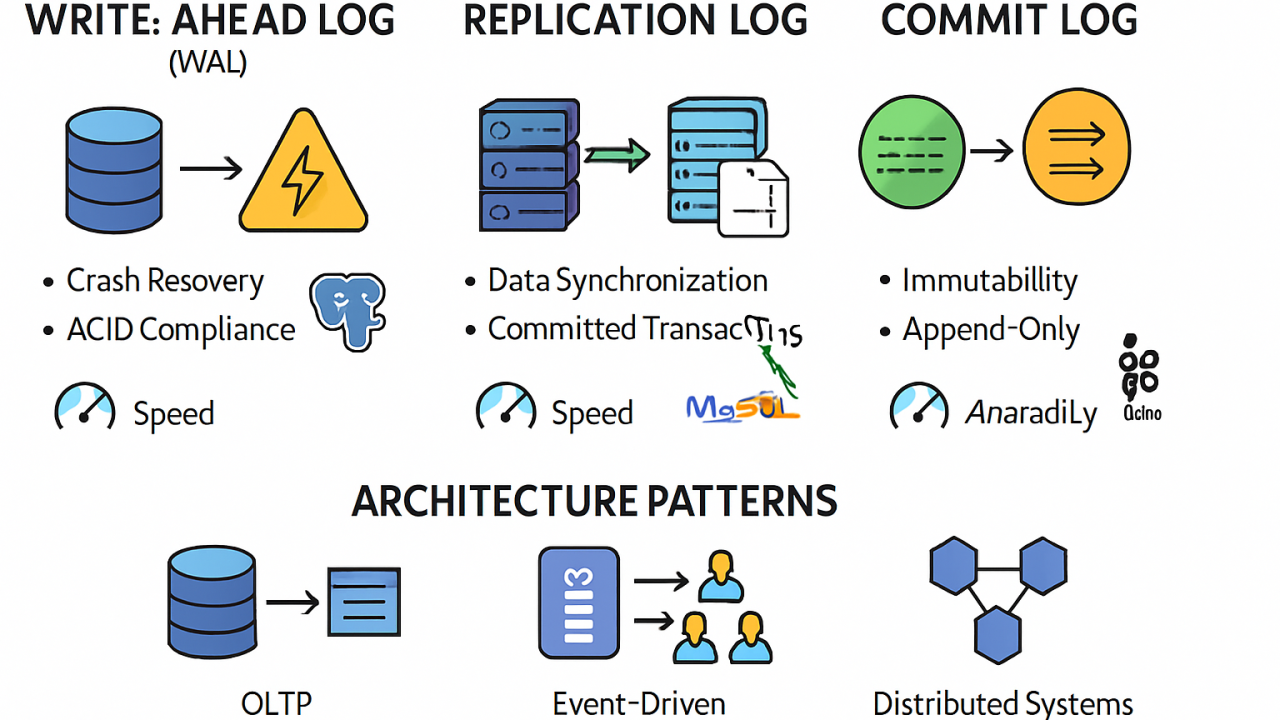
Log completeness under this specification demands three cumulative properties that together constitute sufficient conditions for action enablement. Serialization establishes total ordering through hybrid logical-physical timestamps combining Lamport clocks for distributed causality tracking with hardware-generated nanosecond-precision counters for local ordering. Hashing binds content to sequence position through cryptographic digest functions with preimage resistance, second-preimage resistance, and collision resistance. Local commit requires durable write acknowledgment from tamper-resistant non-volatile memory with write latency below the action release threshold.
Action Taxonomy
API Calls
External interface invocations intercepted at system call boundary
State Changes
Persistent modifications intercepted at memory management unit
Physical Actuation
Energy transfer across cyber-physical boundary
The execution release precondition establishes log existence as necessary condition for action enablement, implemented through verification gate location in the processor pipeline between instruction decode and execution retirement. The irrevocable commitment point occurs when hardware logging subsystem generates attestation quote binding log entry to platform identity and measurement.
III. Cryptographic Actuator Interlock and Execution Coupling
The transformation of logging from background process to protocol-level gate requires fundamental architectural restructuring that eliminates any execution path bypassing logging verification. TML inverts conventional relationships through synchronous insertion into the critical execution path: every action proposal stalls at a hardware-enforced barrier until logging completion is cryptographically verified, with no deferred write patterns, asynchronous notification mechanisms, or optimistic execution with rollback capability permitted.
Cryptographic execution path locking binds proposed actions to prior system state through hash chain construction that makes action authorization contingent on valid log chain maintenance. The Merkle accumulator root serves as execution capability token: this compact representation of entire log history is maintained in hardware-protected registers accessible to execution gate but modifiable only by logging subsystem.
Actuator release imposes three independent cryptographic requirements that must all satisfy before energy transfer across cyber-physical boundary. Valid log hash ensures preimage resistance preventing forgery. Local commit acknowledgment requires hardware-generated attestation quote binding stored log entry to platform identity. Inference containment permits internal computation to proceed without logging overhead, but results cannot propagate to external effect until logging completes.
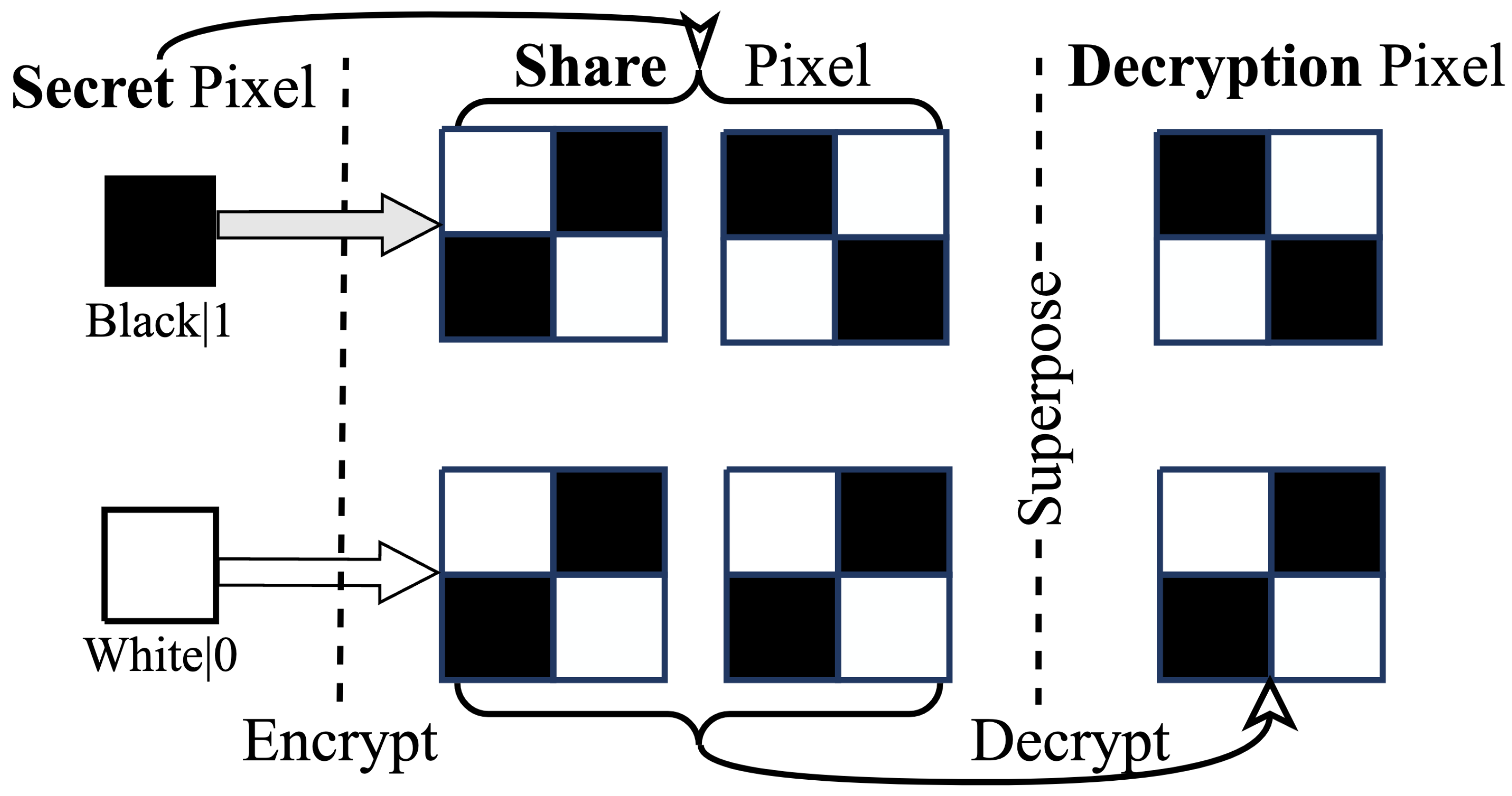
The write-before-execute model adapts proven database techniques to autonomous system execution control. Log entry durability before instruction retirement ensures no instruction with external effect completes before corresponding log acknowledgment from hardware-backed storage. Transactional semantics enforce atomic commit or full abort: partial logging failures cannot enable partial execution.
IV. Hardware Root of Trust
Secure enclave deployment establishes isolated execution environment for logging kernel operations through Trusted Execution Environment technology. TEE isolation boundary ensures logging code executes in hardware-protected domain inaccessible to normal operating system or hypervisor, with memory encryption preventing physical memory probing and bus snooping attacks.
Trusted Platform Module functions extend hardware root of trust to platform-wide integrity measurement. Platform Configuration Registers store extended log hash chain through chained extend operations—the only mechanism to modify register contents—with automatic inclusion in attestation quotes. Quote generation binds log state to TPM identity creating cryptographically verifiable proof of system configuration and logging completeness.
TEE Protection
- Memory encryption
- Remote attestation
- Sealed storage
- Isolation boundary
TPM Integration
- Platform Configuration Registers
- Attestation quotes
- Monotonic counters
- Integrity measurement
Hardware Security Module integration provides highest assurance level for critical logging operations. HSM-hosted signing keys for log entry authentication ensure key material never exists outside hardware-protected boundaries, with all operations occurring within secure execution environment. Rate-limited signing prevents flooding attacks exhausting quotas or triggering automatic destruction.
Software-only enforcement is demonstrably insufficient for invariant guarantee through multiple fundamental attack vectors. Kernel compromise enables direct memory manipulation that can forge log entries, bypass verification checks, or suppress logging entirely while maintaining apparent system operation. Hypervisor escape permits logging bypass by executing at privilege levels above virtualized logging infrastructure.
V. The Sacred Zero / Epistemic Hold
State 0 trigger conditions define circumstances requiring mandatory system pause for epistemic state capture before continuation or escalation. Uncertainty threshold exceeding calibrated confidence bound occurs when internal uncertainty quantification—whether entropy of neural network outputs, variance of ensemble predictions, or explicit Bayesian credible intervals—exceeds thresholds established through validation on representative operational data.
Mandatory state capture ensures hesitation events are fully documented for subsequent analysis and potential model improvement. Full neural activation tensor serialization records complete internal state of neural computation including all layer outputs and attention weights, with compression preserving essential information while respecting storage constraints.
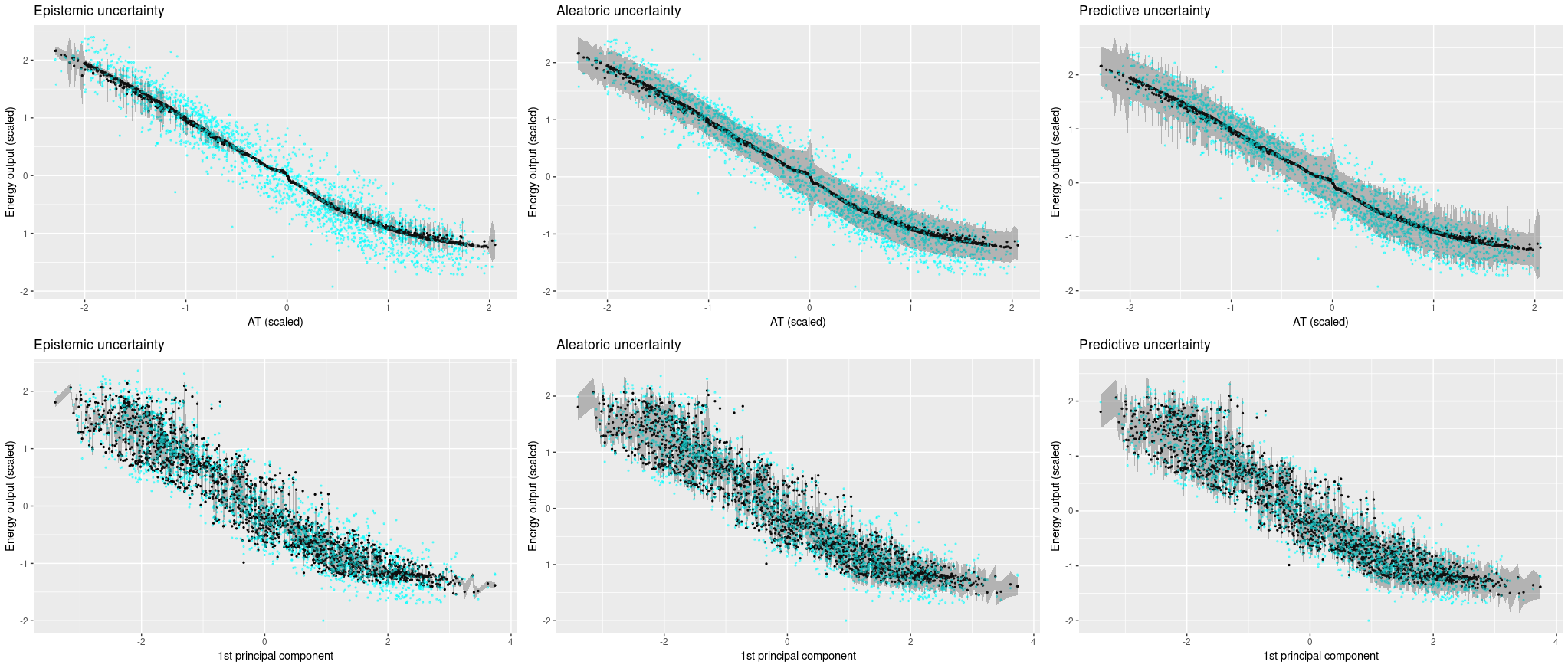
Hesitation event logging requirements enforce invariant compliance even in uncertainty-handling paths. Epistemic state commit before any escalation pathway activation prevents paradox of undocumented uncertainty resolution, where fallback behaviors or human override might activate without preserving record of triggering conditions.
Forced continuation prevention resists external pressure to bypass epistemic holds. External pressure detection via timing analysis identifies artificially accelerated decision demands through statistical detection of anomalous inter-arrival times, triggering enhanced logging and potential State 0 entry.
VI. Cryptographic Non-Repudiation of Action
Verifiable prior log requirement establishes that every action must be cryptographically linked to predecessor log entry, creating chain of evidence from system initialization through current state. Hash chain traversal proving temporal ordering enables efficient verification that action A occurred after log entry L without examining complete history, through Merkle proof techniques providing logarithmic-size evidence of inclusion and ordering.
Invalid execution state definition provides criteria for identifying and responding to accountability violations. Orphaned action without corresponding log entry represents fundamental invariant violation that proper implementation prevents, with detection triggering immediate safe harbor transition and forensic preservation.
Log as behavioral proof enables complete trace reconstruction from genesis to present, with hash chain providing tamper-evident record of all state transitions. Third-party verification without system cooperation ensures accountability does not depend on continued operator cooperation.
Identity-integrity-logging triad binds three critical security properties into unified evidentiary structure. Actor authentication at log entry creation establishes who initiated action, with multi-factor authentication and hardware-backed credentials preventing credential theft and subsequent repudiation.
VII. Failure Modes and System Response
Storage failure response mandates immediate execution halt upon detection of write acknowledgment timeout, with timeout thresholds calibrated to distinguish genuine failures from performance degradation and triggering conservative failure classification. Detection via write acknowledgment timeout identifies failures through absence of expected hardware acknowledgments.
Fail-Closed Mandate
All failure modes default to execution denial with no exception for purported emergencies or diagnostic requirements. Manual override requires physical presence and multi-party authorization.
Hashing failure response addresses cryptographic hardware or software failures compromising verification integrity. Hardware accelerator fault detection identifies failures through built-in self-test procedures, error correction code violations, or anomalous timing.
Queue overflow and backpressure prevents resource exhaustion from compromising invariant enforcement. Admission control rejecting new action proposals implements backpressure at system boundary, with rejection notifications enabling upstream systems to implement appropriate degradation strategies.
Key management failure response addresses critical dependency on cryptographic key availability and integrity. HSM communication loss detection identifies failures through timeout and error code analysis, with detection triggering automatic key failover to redundant HSM infrastructure where available.
VIII. Cyber-Physical Safe Harbor States
"Do nothing" hazard analysis reveals passive safety strategies are inadequate for many physical systems. Momentum continuation in mechanical systems demonstrates that ceasing active control does not achieve safety: vehicles traveling at speed continue moving indefinitely without braking, and uncontrolled coasting may be more hazardous than controlled deceleration.
Safe harbor state definition specifies target conditions for execution denial transitions. Kinetic energy minimization requires achievement of zero velocity for all moving components, with verification through independent sensors and bounded convergence time ensuring safe harbor entry completes before hazard escalation.

Execution denial transition rules govern pathways from normal operation to safe harbor with predictable characteristics. Graceful degradation pathway with time-bounded convergence provides smooth transition for non-imminent hazard scenarios, with convergence time budgeted from failure detection plus safety margin.
Control stability preservation maintains essential system functions during safe harbor residence. Low-level stabilizing controllers independent of decision authority ensure basic stability is maintained even when high-level decision-making is suspended for logging failure or other conditions.
Decision authority separation clarifies relationship between logging gate and control functions. Logging gate controlling high-level goal selection ensures safe harbor entry affects strategic objectives rather than tactical control, with low-level controllers continuing to execute safe harbor maintenance behaviors.
IX. Cryptographic Guarantees
Canonicalization procedures eliminate representation ambiguity that could enable equivocation or verification failure. Deterministic serialization produces identical byte sequences for semantically equivalent log entries, with serialization rules specifying field ordering, encoding standards, and default value handling in exhaustive detail.
Tamper-evidence mechanisms ensure any modification to log content is detectable with overwhelming probability. Hash chain sensitivity to any content modification creates avalanche effect where single-bit changes propagate through entire subsequent chain, with verification requiring complete chain reconstruction that reveals modification location.
Merkle accumulator operations provide efficient verification capabilities for large log volumes. Efficient membership proof generation for individual entries enables logarithmic-size evidence that specific entry is included in accumulator state, with proof verification requiring only public accumulator root and entry content.
Post-commit immutability ensures that once acknowledged, entries cannot be modified or deleted without detection. Write-once storage medium enforcement through hardware or software mechanisms prevents overwrite operations, with enforcement including physical write-protect signals, firmware-level access control, and cryptographic verification on read.
Undetectable modification impossibility establishes ultimate security guarantee for log integrity. Collision resistance of hash function preventing content substitution ensures adversaries cannot craft malicious entries producing identical hashes to legitimate entries, so any content change necessarily changes hash.
X. Adversarial Resistance
Logging suppression countermeasures address deliberate attempts to prevent log generation or persistence. Redundant logging channels with Byzantine fault tolerance ensure suppression of minority of channels cannot prevent log commitment, with channel diversity including independent hardware, software, and administrative domains.
Execution bypass prevention closes architectural vulnerabilities that could permit action without logging. Hardware gate bypass requiring physical modification ensures software attacks cannot circumvent logging verification, with physical security measures including tamper detection and response designed to complete before successful extraction.
Replay and forgery defenses prevent adversaries from creating fraudulent log entries or reusing legitimate ones inappropriately. Nonce inclusion preventing exact log entry replay ensures each entry is unique and cannot be duplicated to create false history, with nonce sources including hardware random number generators and monotonic counters.
Insider threat mitigation addresses elevated risk from parties with legitimate system access. Multi-party authorization for administrative functions ensures no single individual can compromise logging integrity, with authorization schemes providing collusion resistance through threshold structures.
Privileged attack surface reduction minimizes code and access paths available to high-privilege operations. Minimal trusted computing base for logging kernel limits code subject to correctness proof, with kernel size measured in thousands rather than millions of lines enabling comprehensive formal analysis.
Silent action prevention ensures unlogged behavioral deviation is detectable through independent means. Observable energy consumption correlation with logged activity enables physical verification that system activity matches log record, with power analysis detecting anomalous consumption patterns suggesting hidden computation.
XI. Integration with Dual-Lane Architecture
Fast lane sub-2ms commitment provides latency-critical path for safety-relevant autonomous system operations. Dedicated hardware pipeline bypassing general-purpose operating system eliminates software scheduling and context switch overhead, with pipeline implementation in FPGA or ASIC technology achieving deterministic latency bounded by physical propagation delays.
Slow lane asynchronous anchoring provides eventual global verifiability without constraining fast lane latency. Batch compression and cryptographic aggregation reduces bandwidth and storage requirements for external publication, with aggregation techniques preserving individual entry verifiability through Merkle inclusion proofs.
Durability versus public proof separation clarifies distinct guarantees provided by each lane. Fast lane guaranteeing local crash recovery ensures system restart can reconstruct consistent state from local storage alone, without requiring external connectivity or cooperation.
Anchoring delay invariant compliance maintains that action release depends only on fast lane commitment, with slow lane timing not affecting execution authorization. Action release dependent only on fast lane commitment maintains latency independence from slow lane performance.
Backpressure and circuit breaker behavior prevents fast lane overload from cascading to system failure. Fast lane queue depth monitoring with admission control rejects new action proposals when queue approaches capacity, with depth thresholds calibrated to maintain latency bounds for accepted entries.
Implementation Requirements
The "No Log = No Action" invariant represents a fundamental shift from conventional optional logging to mandatory invariant enforcement through cryptographic actuator interlock. This specification establishes binding architectural constraints that cryptographically couple all execution to prior log commitment, with hardware-enforced gates, fail-closed behavior, and dual-lane architecture achieving sub-2ms commitment latency while maintaining global verifiability. The implementation must treat these principles as non-negotiable system laws, with no administrative override capability and universal fail-closed semantics ensuring that transparency becomes an active system constraint rather than passive property.