Universal Scalability of Ternary Moral Logic
Under the "No Spy, No Weapon" Mandate
A comprehensive analysis of architectural constraints, geopolitical pressures, and economic viability for ethical AI deployment
Executive Summary
TL;DR: TML's NoS-NoW mandate is technically feasible with hard architectural constraints, economically viable only with substantial alternative market development, and politically unrealistic for universal adoption under current geopolitical conditions.
The Ternary Moral Logic (TML) framework's ambitious prohibition on lethal targeting, autonomous weapons, and mass civilian surveillance faces a fundamental tension between technical integrity and market adoption. Our comprehensive analysis reveals that while the "No Spy, No Weapon" (NoS-NoW) mandate can be architecturally enforced through Sacred Zero, Sacred Pause, and cryptographic audit logging, universal scalability confronts insurmountable geopolitical and economic barriers.
Technical feasibility is the strongest pillar: current secure element technology (TPM, HSM) provides adequate foundation for hardware-enforced constraints, and cryptographic audit logging can achieve legal admissibility standards. However, hardware supply chain integrity remains an unresolved vulnerability against state-level adversaries.
Economic viability requires alternative markets to replace 25-35% of global AI revenue currently concentrated in defense, intelligence, and surveillance applications. While healthcare, climate modeling, and finance compliance offer $50-75 billion in potential 2030 revenue, replacement ratios max out at 92% under optimistic scenarios, leaving structural deficits.
Political realism presents the most significant barrier: the February 2026 Anthropic-Pentagon confrontation demonstrates that state actors will invoke Defense Production Act authority, supply chain risk designation, and classified network access denial to compel mandate modification. Democratic governments consistently create national security exceptions, and major powers perceive unilateral constraint as strategic vulnerability.
Technically Feasible
Hardware-enforced constraints and cryptographic auditing provide viable enforcement mechanisms
Economically Challenged
25-35% market exclusion requires substantial alternative revenue development
Politically Unrealistic
State pressure and geopolitical resistance prevent universal adoption
I. Precise Domain Boundary Validation
Lethal Targeting Prohibition
Technical Criteria
- Output type analysis for target coordinates
- Downstream action chain monitoring
- Predictable effects on human life assessment
The prohibition extends beyond weapons release to the entire targeting chain: sensor fusion, behavioral analysis, geolocation correlation, and battle damage assessment. The March 2020 Libya incident with the Turkish Kargu-2 drone demonstrates the operational reality TML seeks to prevent.

U.S. Replicator Initiative
The Pentagon's plan to field "attributable, autonomous systems at a scale of multiple thousands" within 18-24 months directly confronts TML constraints.
Edge Case Adjudication
Dual-Use Analytics Platforms
Palantir's AI Platform exemplifies the civilian-military boundary challenge. The February 2026 Anthropic-Palantir confrontation demonstrates operational integration risks.
Defensive Cybersecurity
Purely passive defenses are permitted, but active defenses that penetrate external systems cross into prohibited territory.
Satellite Image Analysis
Environmental monitoring is permitted, but identification of military targets with engagement precision is prohibited.
Predictive Policing
Categorically prohibited due to structural bias amplification and circumvention of probable cause requirements.
II. Universality Stress Test
Technical Interoperability Across Jurisdictions
Sacred Pause Latency
Mandatory deliberation period creates latency intolerable for real-time systems like missile defense and autonomous vehicles.
Cryptographic Audit Logs
National data localization requirements conflict with distributed verification needs for tamper resistance.
Protocol Standardization
Moral Trace Log formats and verification protocols require multilateral agreement that current geopolitical conditions don't support.
Economic Viability Without Defense Sector Revenue
Revenue Gap Analysis
TML excludes 25-35% of global AI market, concentrated in the highest-value segments with 35%+ projected CAGR.
Market Exclusion Concentration
Political Adoptability by Democratic Governments
National Security Exception Pressure
The February 2026 Anthropic-Pentagon confrontation demonstrates the intensity of state pressure: Defense Production Act invocation threat, supply chain risk designation, and classified network access denial.
Legislative Sovereignty
Constitutional principles resist "irreversible" policy commitments that bind future legislative majorities.
Executive Flexibility
Emergency authority claims override technical constraints during perceived existential threats.
Alliance Integration
Five Eyes and NATO interoperability requirements pressure capability maximization.
III. Power Pressure Simulation
State Actor Exemption Demand Scenarios
National Security Framing Typologies
Imminent Threat
"Delay enables catastrophic attack" - exploits emergency authority override
Competitive Disadvantage
"Adversary unconstrained development" - exploits strategic anxiety
Alliance Obligation
"Treaty commitments require capability" - exploits institutional commitment

Escalation Ladder
Legal Mechanisms for Compelled Participation
Defense Production Act Invocation
Broad presidential authority to compel industrial production for national defense, explicitly threatened in the Anthropic-Pentagon confrontation.
Supply Chain Risk Designation
Creates secondary effects beyond direct contract exclusion: contractor relationship termination, commercial partner reluctance, and financial market access degradation.
Technical Resistance Strength
Sacred Zero Hardware-Enforcement Feasibility
Implementation Levels
Remaining Vulnerabilities
- • Hardware supply chain compromise
- • State-level manufacturer compulsion
- • Physical access attacks
- • Cryptographic algorithm obsolescence
Cryptographic Audit Logs
Tamper-evident design with legal admissibility under Federal Rules of Evidence
Distributed Verification
Multi-party consensus mechanisms resist single-point compromise
Verdict
Strong but imperfect resistance against state-level adversaries
Structured Risk Matrix
| Threat Actor | Capability | Intent | Risk Score |
|---|---|---|---|
| U.S. Government | Very High | High | Critical (12) |
| Chinese Government | High | High | High (9) |
| Corporate Competitors | High | High | High (9) |
| Russian Government | Medium | Medium | Moderate (6) |
| Criminal/Non-State | Medium | Low-Medium | Moderate (4) |
IV. Economic Sustainability Model
Excluded Revenue Streams
FY2026 NDAA Market Acceleration Impact
The U.S. FY2026 NDAA's fast-track defense AI provisions create massive market acceleration that TML explicitly forgoes, with projected doubling of Pentagon AI spending.
Market Exclusion Breakdown
Critical Insight
Government AI contracts offer premium pricing, long-term stability, and technology development funding that commercial markets rarely match, making replacement particularly challenging.
Alternative High-Value Domain Modeling
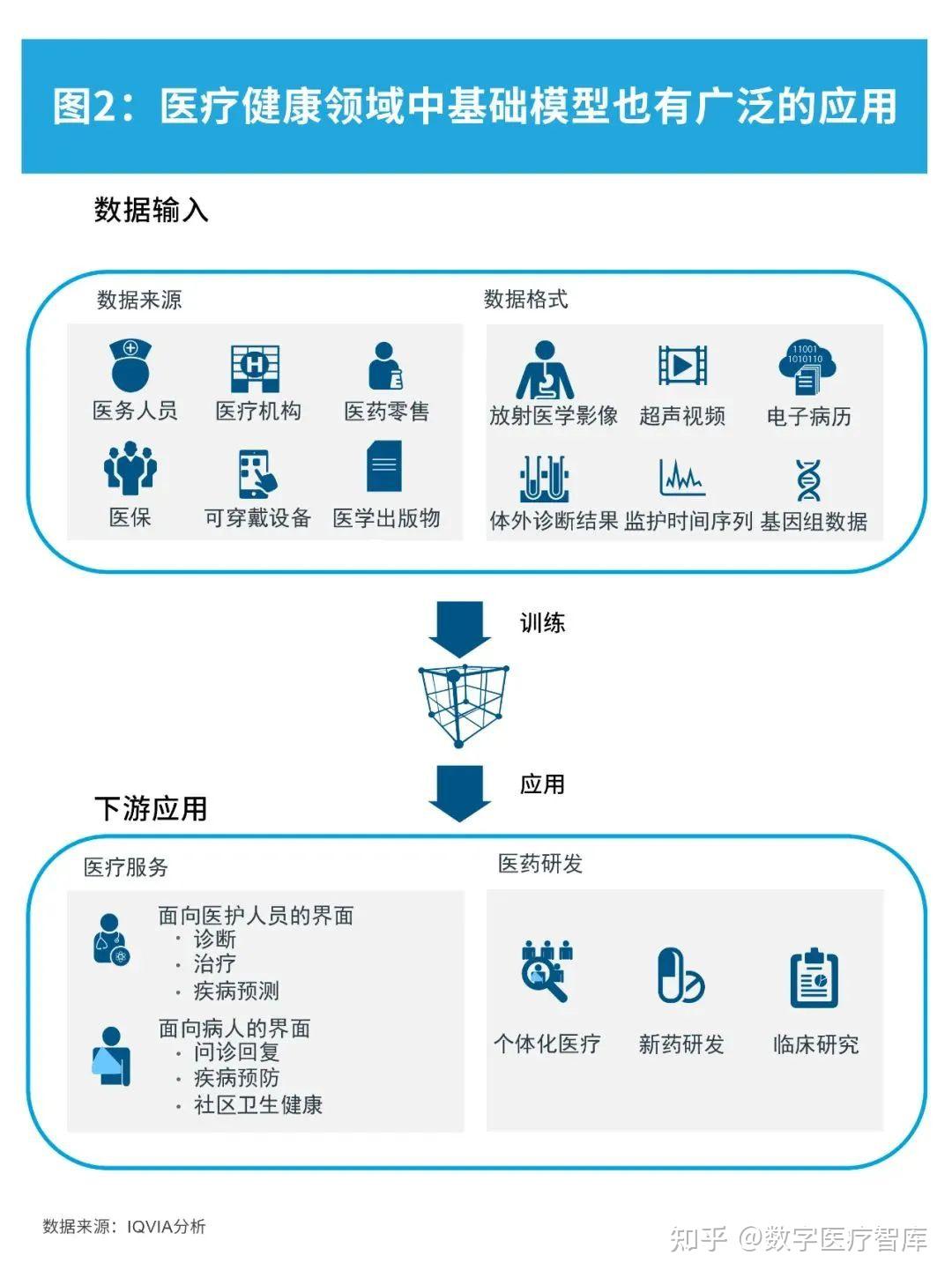
Healthcare
- • Diagnostic AI explainability
- • Drug discovery reproducibility
- • Clinical trial optimization
Climate Modeling
- • Earth system simulation
- • Carbon accounting verification
- • Climate risk analytics
Finance Compliance
- • AML explainability requirements
- • Regulatory reporting automation
- • Algorithmic trading oversight
Revenue Replacement Assessment
V. Governance Integrity Evaluation
Civil Society Reception
Public Opinion & Survey Data
NGO & Advocacy Alignment
Critical Gap
Civil society has mobilized for policy constraints but has limited capacity to evaluate or promote technical enforcement mechanisms.
Enterprise Adoption Hesitation
Liability Exposure Concerns
Competitive Disadvantage Anxiety
Insurance and Risk Transfer Market Development
National Security Objections
Military Effectiveness Arguments
OODA Loop Compression
Military doctrine emphasizes reducing the decision cycle from observation to action as a source of competitive advantage. TML's Sacred Pause directly contradicts this imperative.
Force Protection Imperative
Autonomous systems are justified by reducing personnel risk in hostile environments. TML constraints may increase human exposure.
Alliance Friction Points
Geopolitical Resistance
VI. Comparative Framework Review
Responsible AI Principles
Major AI Labs (OpenAI, Anthropic)
OECD AI Principles
Regulatory Frameworks
EU AI Act
Defense AI Ethics Frameworks
Comparative Positioning Matrix
| Framework | Enforcement | Military AI | Surveillance | Binding Status |
|---|---|---|---|---|
| TML + NoS-NoW | Hardware | Prohibited | Prohibited | Architectural |
| EU AI Act | Legal | Exempt | Restricted | Regulatory |
| OECD Principles | Voluntary | Flexible | Guidance | Non-binding |
| DoD AI Ethics | Policy | Permitted | Permitted | Procedural |
Strategic Positioning
TML occupies a unique position as the most stringent framework with architectural enforcement. While this creates adoption barriers, it provides competitive differentiation in trust-sensitive markets and potential "Technical Backbone" role for regulatory compliance.
VII. Gray Zone Elimination
Identified Ambiguity Vectors
Dual-Use Platform Exploitation
Civilian platforms like Palantir's AI system can be rapidly repurposed for military targeting through operational integration.
Humanitarian Pretext
Disaster response justification for autonomous systems that develop capabilities transferable to combat operations.
Active Defense Characterization
Operations described as defensive that cause effects indistinguishable from offensive operations.
Intelligence vs. Targeting
Systems providing "strategic awareness" that in fact enable precise targeting through operational integration.
Structural Reinforcement Mechanisms
Technical Enforcement Hierarchy
Prevention Mechanisms
Detection Mechanisms
Third-Party Verification Architecture
Certification Process
- • Hardware specification verification
- • Software integrity validation
- • Use-case boundary confirmation
- • Tamper resistance assessment
Continuous Monitoring
- • Real-time behavioral analysis
- • Anomaly detection triggers
- • Periodic re-certification
- • Version control verification
Compliance Enforcement
- • Automatic Sacred Zero triggers
- • Public attestation requirements
- • Revocation for violations
- • Legal liability framework
VIII. Final Determination
Can TML achieve universal scope while maintaining categorical prohibitions?
Technically Feasible
Hardware-enforced constraints and cryptographic auditing provide viable enforcement mechanisms with current technology.
Economically Challenged
25-35% market exclusion requires substantial alternative market development with uncertain replacement ratios.
Politically Unrealistic
State pressure, geopolitical resistance, and democratic sovereignty concerns prevent universal adoption under current conditions.
Conditions Required for Universality
Geopolitical Convergence
Major powers must converge on equivalent constraints, reducing strategic autonomy concerns.
Market Development
Alternative markets must reach 60-80% revenue replacement to sustain comparable investment levels.
Multilateral Endorsement
Network effects from regulatory integration create competitive advantages offsetting constraint costs.
Adoption Velocity Forecast (2025-2040)
- • EU AI Act implementation
- • Technical standard development
- • Civil society mobilization
- • Healthcare market entry
- • Finance compliance adoption
- • Climate modeling applications
- • Allied coordination attempts
- • Standards competition intensifies
- • Market bifurcation solidifies
- • Democratic bloc standardization
- • Persistent geopolitical resistance
- • Limited universality achievement
Strategic Recommendations
For TML Implementation
- Focus on EU market as "Safe Haven" for civilian AI deployment
- Develop healthcare and finance compliance markets aggressively
- Build civil society partnerships for legitimacy and advocacy
- Prepare for state pressure with distributed organizational structure
For Policy Stakeholders
- Recognize TML as potential "Technical Backbone" for EU AI Act implementation
- Address hardware supply chain integrity vulnerabilities through policy
- Coordinate multilateral standards to reduce strategic autonomy concerns
- Develop insurance and risk transfer mechanisms for ethical AI adoption
Final Assessment
Ternary Moral Logic represents the most technically rigorous approach to ethical AI constraints, but faces insurmountable geopolitical and economic barriers to universal adoption under current conditions. The framework's future lies not in global dominance, but as a "Safe Haven" standard for democratic jurisdictions willing to accept competitive constraints for ethical integrity.